| View previous topic :: View next topic |
| Author |
Message |
Berrit
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 25 Jun 2018
Posts: 2
|
 Posted: Tue Jun 26, 2018 3:33 am Post subject: Need help with AOB injection Posted: Tue Jun 26, 2018 3:33 am Post subject: Need help with AOB injection |
 |
|
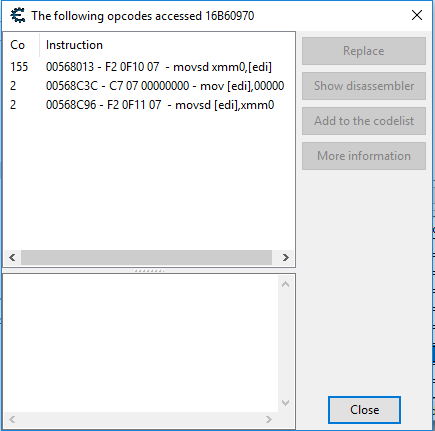
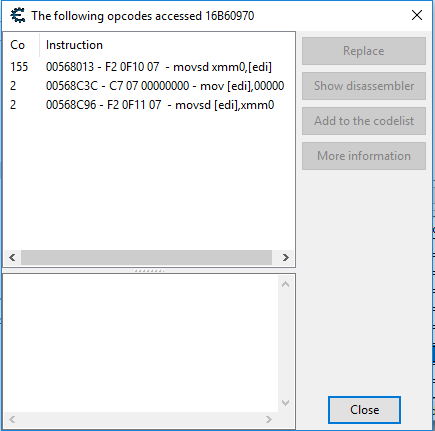
The game I'm trying to create a table for updates very frequently so i read the tutorials on AOB injection and thought i would give it a try. When i got to the part about finding out what accesses the address i got the posted image. I used two of the items in question which each added 1 count. None of these quite seem to work. I also checked each of them to see what addresses each instruction accesses and there were a lot for each one. I'm unsure what to do.
I understand how to make pointers that persist as long as the game doesn't update.
| Description: |
|
| Filesize: |
10.46 KB |
| Viewed: |
7032 Time(s) |
|
|
|
| Back to top |
|
 |
OldCheatEngineUser
Whateven rank
 Reputation: 20 Reputation: 20
Joined: 01 Feb 2016
Posts: 1586
|
 Posted: Tue Jun 26, 2018 3:56 am Post subject: Posted: Tue Jun 26, 2018 3:56 am Post subject: |
  |
|
seems to be movsd [edi],xmm0 moving double floating point value. (hopefully not graphical value)
since the instruction accessing bunch of addresses, then you have 5 ways to do it:
see what addresses this instruction accesses:
- compare register states for 3-5 addresses
- open the addresses in dissect data structure
- use structure compare
- structure spider
- use pointer in your script
way 6 (exceptional)
if the previous subroutine is used only for the player, then you can prevent the call.
using pointer in script example:
| Code: | mov [ebx+00000480],eax
push edx
push ecx
lea ecx,[ebx+480]
lea edx,[[[[[["Tutorial-i386.exe"+001506E0]+584]+248]+c]+11c]+6c0]
cmp ecx,edx
cmove eax,[CEtut]
mov [ebx+480],eax
pop ecx
pop edx |
this is my script for ce tut first step, just an example to provide ... for using pointers in script to compare.
_________________
About Me;
I Use CE Since Version 1.X, And Still Learning How To Use It Well!
Jul 26, 2020
| STN wrote: | | i am a sweetheart. |
|
|
| Back to top |
|
 |
Berrit
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 25 Jun 2018
Posts: 2
|
 Posted: Wed Jun 27, 2018 12:54 am Post subject: Posted: Wed Jun 27, 2018 12:54 am Post subject: |
 |
|
| Wow i am so confused lol. The pointers i was trying to make were for inventory items so i could modify the amounts if that matters. Are there any videos or tutorials to help me work on this? Or keywords and things i could search. I'm not against doing work myself, just need a direction to go.
|
|
| Back to top |
|
 |
FreeER
Grandmaster Cheater Supreme
![]() Reputation: 53 Reputation: 53
Joined: 09 Aug 2013
Posts: 1091
|
 Posted: Wed Jun 27, 2018 11:11 am Post subject: Posted: Wed Jun 27, 2018 11:11 am Post subject: |
 |
|
Typically functions that change many unrelated values are passed arguments relating to how to change the values in which case there is another option which is to "backtrace" to see who calls that function for the value you want (typically making use of conditional breakpoints) and hook that function instead of the more generic one.
As for direction a lot of dealing with instructions that affect multiple values use the keywords "shared opcodes" or "shared instructions" most of which probably use the data dissect or register method, Stephen had a video on using stack values for gamemaker games https://www.youtube.com/watch?v=5fJFSOPGZyQ which are notorious for having many things going through one instruction.
As for AOBs, I'm not sure there's any that really goes into any depth, they're a pretty simple concept. Just scanning for the bytes in memory, typically that represent the assembly instructions to execute. So it's really just a matter of trying to pay attention to the instructions you're creating an AOB for and seeing which bytes refer to constant values like static addresses and offsets that are more likely to change in an update and knowing that jumps and calls are (often) encoded using offsets from the instruction location to where to go. readmem goes along with getting and using those values, see Chris' recent video https://www.youtube.com/watch?v=mBZV3Y-qo_o
and yeah, there's a lot to it 
edit: The pointer example OldCheatEngineUser gave will only work if the pointers don't change during runtime since CE will assemble it into a constant address when the script is enabled, in that case you'd need to separate each offset into a separate read instruction using mov (and possibly lea) which would be done every time the hook was executed.
_________________
|
|
| Back to top |
|
 |
|

 Reputation: 20
Reputation: 20