| View previous topic :: View next topic |
| Author |
Message |
Mystic974
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 27 May 2020
Posts: 8
|
 Posted: Wed May 27, 2020 5:21 pm Post subject: [HELP] DW 3 XL//OAB scan issue Posted: Wed May 27, 2020 5:21 pm Post subject: [HELP] DW 3 XL//OAB scan issue |
 |
|
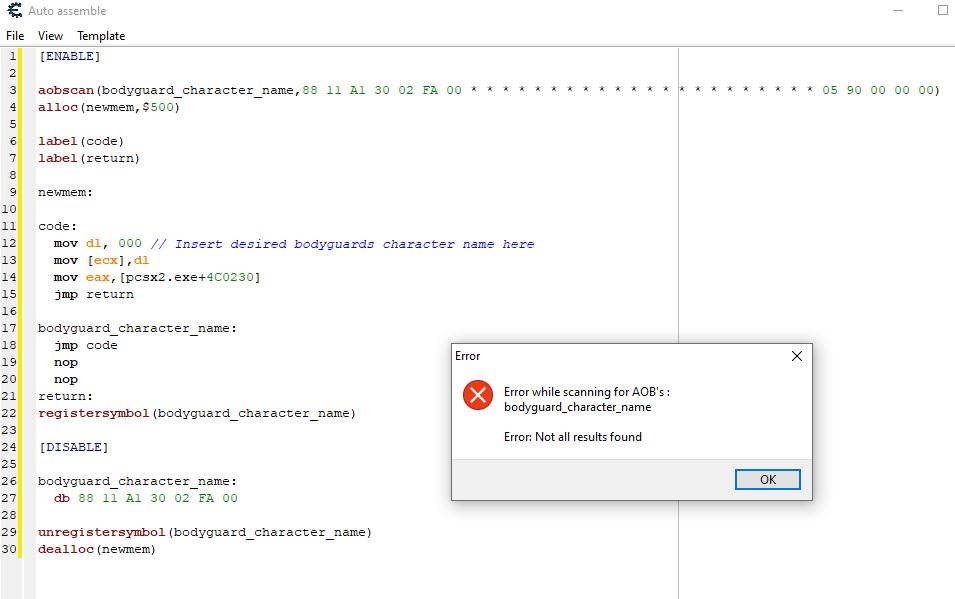
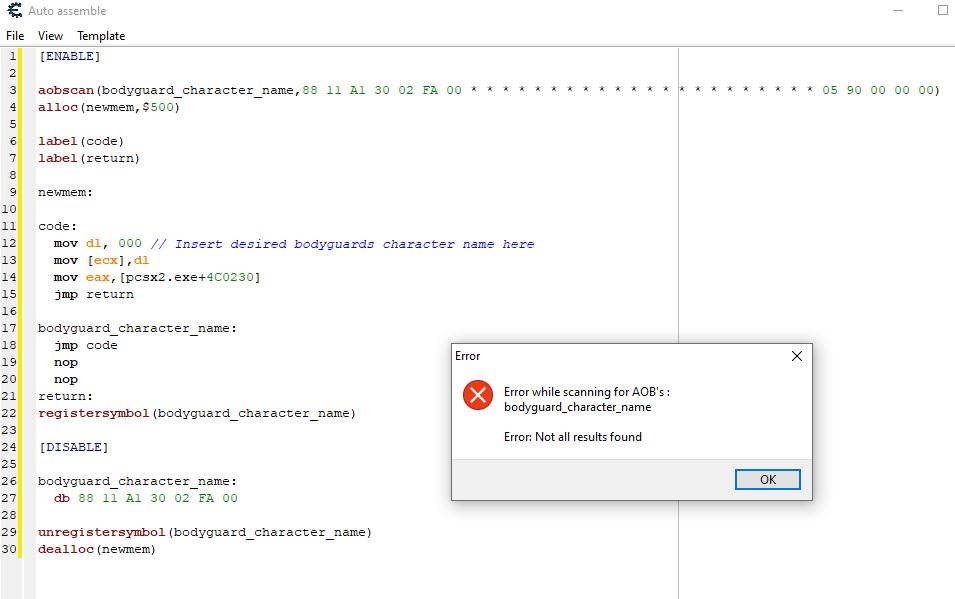
Hello,I'm a total beginner in coding/using cheat engine,I've read many guides but I'm still confused.And there im stuck with a problem.
I'm playing Dynasty Warriors 3 Xtreme legend on PCSX2 and have a cheat table,most of the scripts works,but one that I absolutely want simply don't...
Please I need help step by step to solve that issue...
My cheat engine version : 7.0
Thank you all in advance
| Description: |
|
| Filesize: |
61.98 KB |
| Viewed: |
3369 Time(s) |
|
Last edited by Mystic974 on Wed May 27, 2020 6:00 pm; edited 1 time in total |
|
| Back to top |
|
 |
AylinCE
Grandmaster Cheater Supreme
 Reputation: 32 Reputation: 32
Joined: 16 Feb 2017
Posts: 1253
|
 Posted: Wed May 27, 2020 5:41 pm Post subject: Posted: Wed May 27, 2020 5:41 pm Post subject: |
 |
|
Do the stars have any meaning?
| Code: | | 88 11 A1 30 02 FA 00 * * * * * * * * * * * * * * * * * * * * * * 05 90 00 00 00 |
Why isn't this code like this?
| Code: | | 88 11 A1 30 02 FA 00 ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? 05 90 00 00 00 |
or
| Code: | | 88 11 A1 30 02 FA 00 ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? 05 90 00 00 00 |
_________________
|
|
| Back to top |
|
 |
Mystic974
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 27 May 2020
Posts: 8
|
 Posted: Wed May 27, 2020 5:48 pm Post subject: Posted: Wed May 27, 2020 5:48 pm Post subject: |
 |
|
Thanks for the repply ! Well I don't know,someone gave me this cheat table like that :/ But it's not a problem for the other scripts that look similar to the one on the screenshot,with the stars ,and they works fine.
EDIT : I tried to replace each stars with "??",and I had the same error that popped up 
|
|
| Back to top |
|
 |
Corroder
Grandmaster Cheater Supreme
 Reputation: 75 Reputation: 75
Joined: 10 Apr 2015
Posts: 1667
|
 Posted: Wed May 27, 2020 7:50 pm Post subject: Posted: Wed May 27, 2020 7:50 pm Post subject: |
 |
|
How with adding preserve memory allocation?
| Code: | | alloc(newmem,$1024) |
_________________
Stealing Code From Stolen Code...
And Admit It.. Hmmm....Typically LOL |
|
| Back to top |
|
 |
ParkourPenguin
I post too much
 Reputation: 140 Reputation: 140
Joined: 06 Jul 2014
Posts: 4289
|
 Posted: Wed May 27, 2020 8:25 pm Post subject: Posted: Wed May 27, 2020 8:25 pm Post subject: |
 |
|
Asterisks can be used as wildcards too.
Allocating more memory for newmem won't fix the aobscan pattern not being found. It's not like those few instructions come anywhere near 0x500 bytes anyway.
If the emulator uses jit compilation, you may need to play the game and do different actions in the game to get the correct code to compile.
Otherwise, find the new injection point. Maybe it still accesses pcsx2.exe+4C0230: add that address to the address list and look at what accesses it.
Even if you do get it working, I have no idea what that injection is supposed to do. All it does is replace a character with a null byte. There's nowhere to specify a name- just a single character.
_________________
I don't know where I'm going, but I'll figure it out when I get there. |
|
| Back to top |
|
 |
Mystic974
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 27 May 2020
Posts: 8
|
 Posted: Thu May 28, 2020 5:37 am Post subject: Posted: Thu May 28, 2020 5:37 am Post subject: |
 |
|
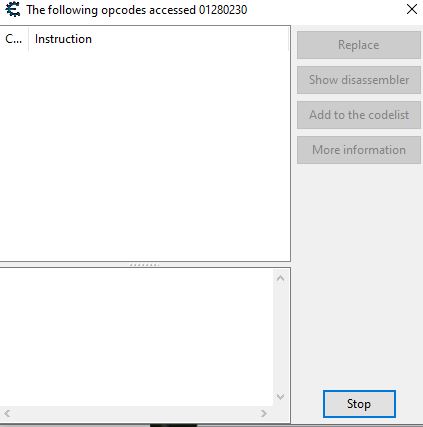
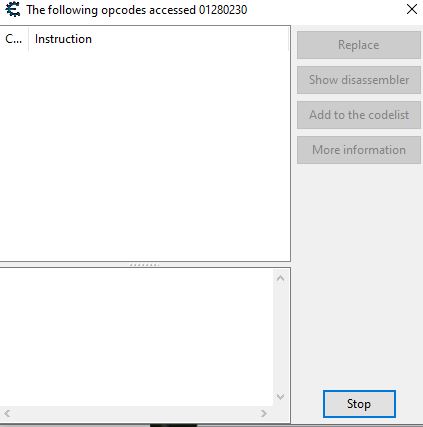
| ParkourPenguin wrote: | | Maybe it still accesses pcsx2.exe+4C0230: add that address to the address list and look at what accesses it. |
Do I have to use pointers?If yes,which one?
| ParkourPenguin wrote: | | Even if you do get it working, I have no idea what that injection is supposed to do. All it does is replace a character with a null byte. There's nowhere to specify a name- just a single character.. |
The injection is used to change the class of the bodyguards in the game : You can have playable characters as bodyguards for example ,and changing the value of the adress between 0-255 will change the bodyguards model/name(255 is the number of characters in the game,playable or not)
| Description: |
| [quote="ParkourPenguin"]Maybe it still accesses pcsx2.exe+4C0230: add that address to the address list and look at what accesses it.[/quote] I got a blank window :/ |
|
| Filesize: |
21.36 KB |
| Viewed: |
3286 Time(s) |
|
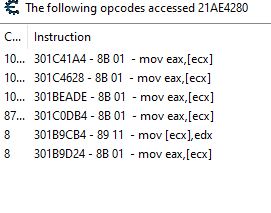
| Description: |
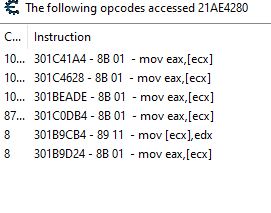
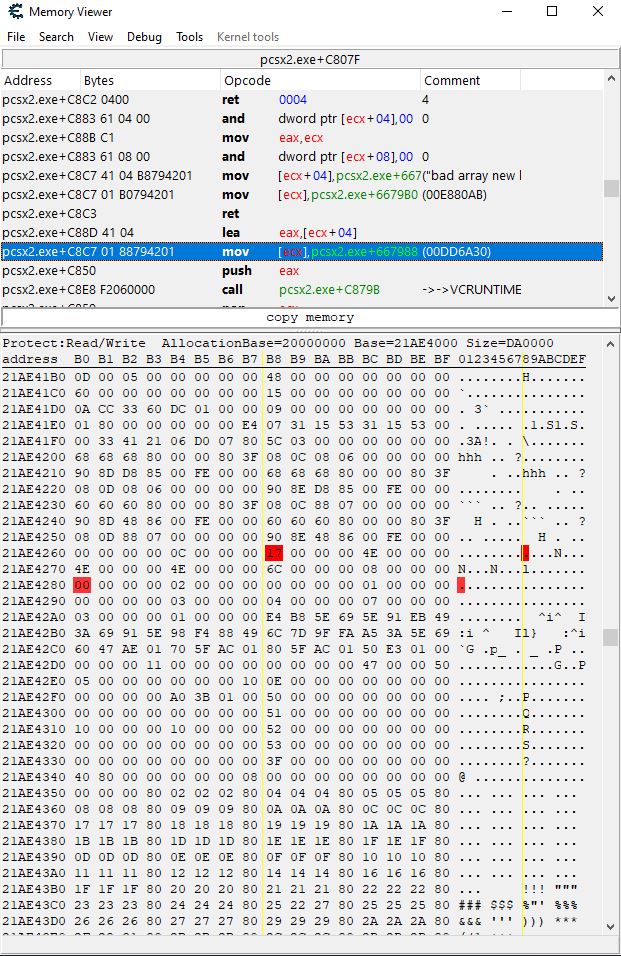
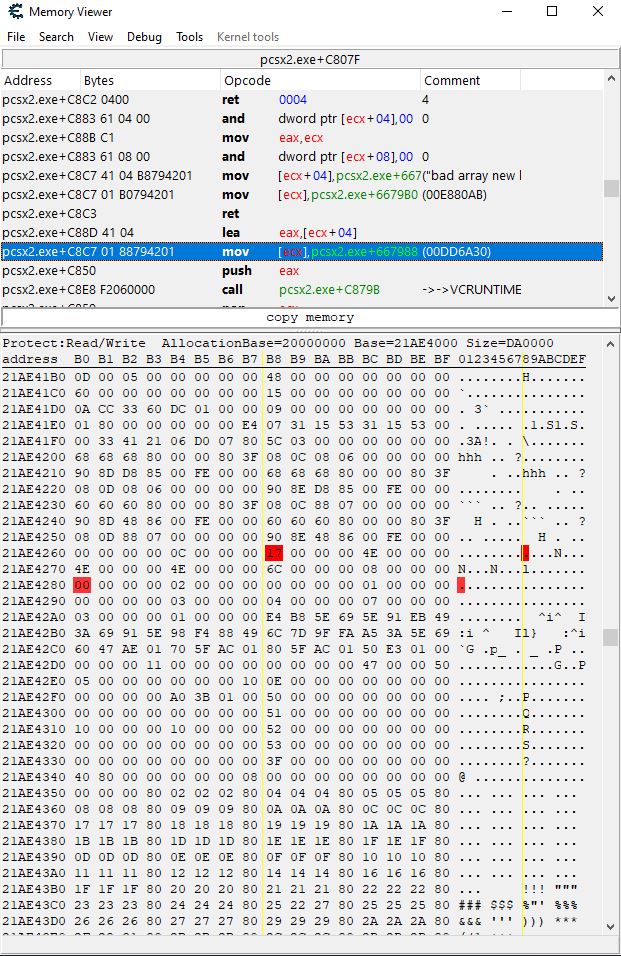
| I used the basic CE scan by changing the number of bodyguards(I don't know if this adress is usefull but there is cleary something about bodyguards ),until I found out an adress,then I used Found out what accesses this adress(nothing to see with character |
|
| Filesize: |
22.29 KB |
| Viewed: |
3286 Time(s) |
|
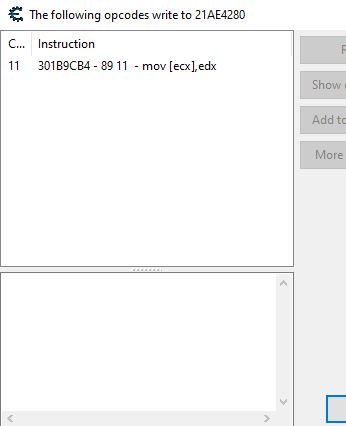
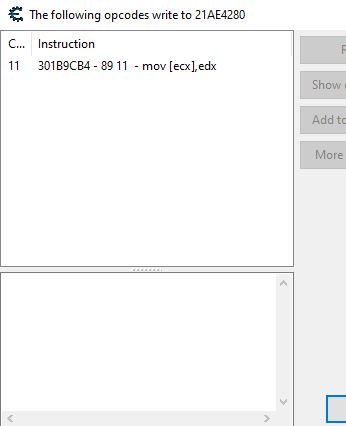
| Description: |
| Same adress but this time Found out what writes this adress |
|
| Filesize: |
19.23 KB |
| Viewed: |
3286 Time(s) |
|
| Description: |
| I browse mem with the adress that I found using number of bodyguards |
|
| Filesize: |
220.44 KB |
| Viewed: |
3286 Time(s) |
|
| Description: |
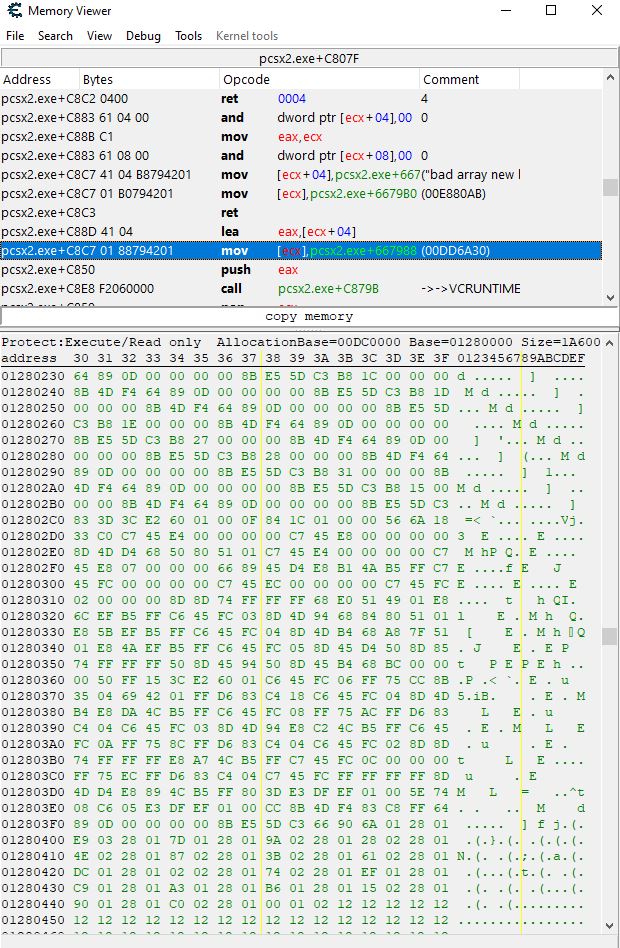
| This is what I got when browsing mem of pcsx2.exe+4C0230 adress |
|
| Filesize: |
187.22 KB |
| Viewed: |
3286 Time(s) |
|
Last edited by Mystic974 on Fri May 29, 2020 9:10 am; edited 1 time in total |
|
| Back to top |
|
 |
atom0s
Moderator
 Reputation: 198 Reputation: 198
Joined: 25 Jan 2006
Posts: 8517
Location: 127.0.0.1
|
 Posted: Thu May 28, 2020 5:49 pm Post subject: Posted: Thu May 28, 2020 5:49 pm Post subject: |
 |
|
This is not Lua related; moved to proper section.
_________________
- Retired. |
|
| Back to top |
|
 |
Mystic974
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 27 May 2020
Posts: 8
|
 Posted: Thu May 28, 2020 5:50 pm Post subject: Posted: Thu May 28, 2020 5:50 pm Post subject: |
 |
|
| atom0s wrote: | | This is not Lua related; moved to proper section. |
Sorry :/
|
|
| Back to top |
|
 |
ParkourPenguin
I post too much
 Reputation: 140 Reputation: 140
Joined: 06 Jul 2014
Posts: 4289
|
 Posted: Thu May 28, 2020 11:21 pm Post subject: Posted: Thu May 28, 2020 11:21 pm Post subject: |
 |
|
Without more information on the code in the original injection point it could be hard to find it.
If you can find this 0-255 value, look at what instructions write to it and you should find something to use as an injection point.
Scanning for fewer bytes of the original injection point might work, but you don't have much to go on.
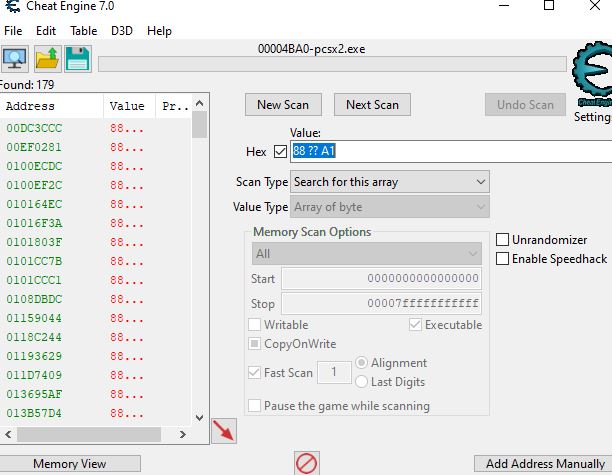
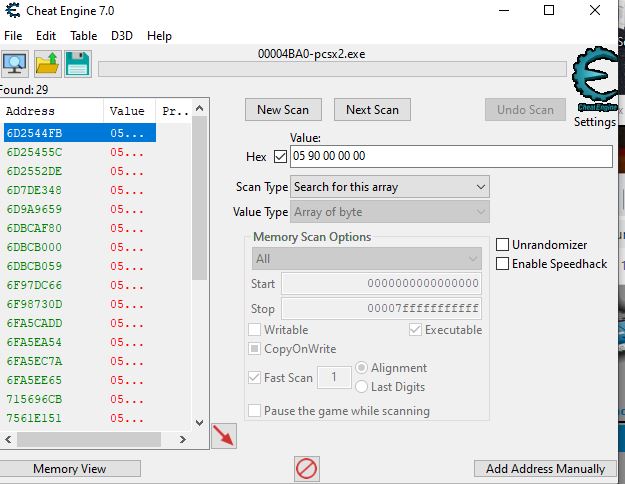
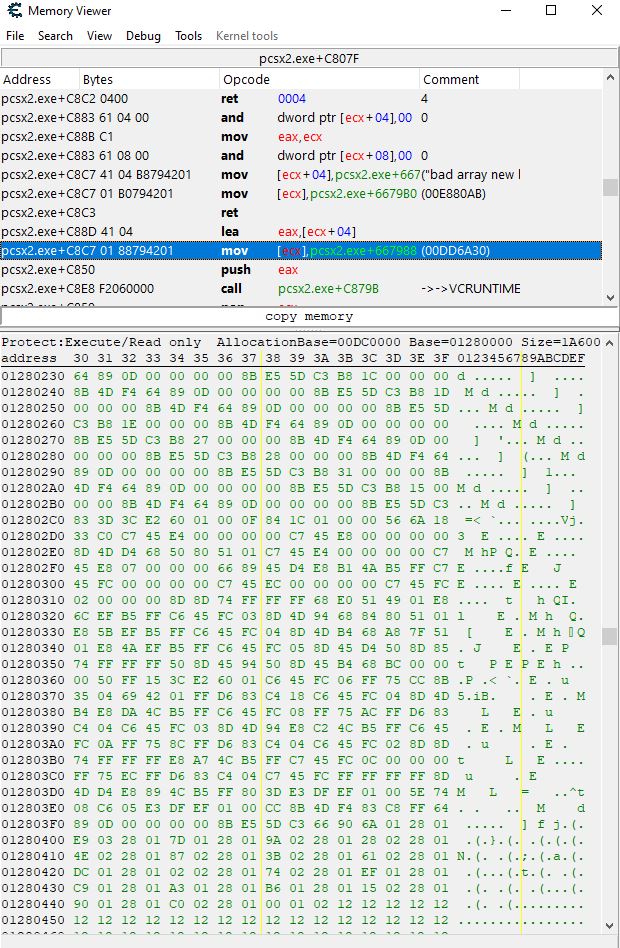
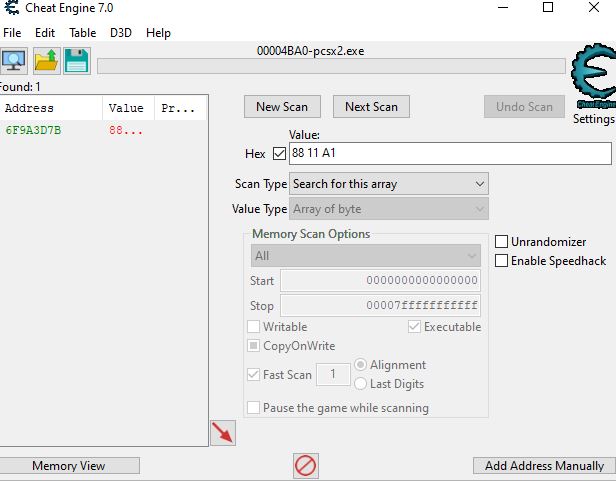
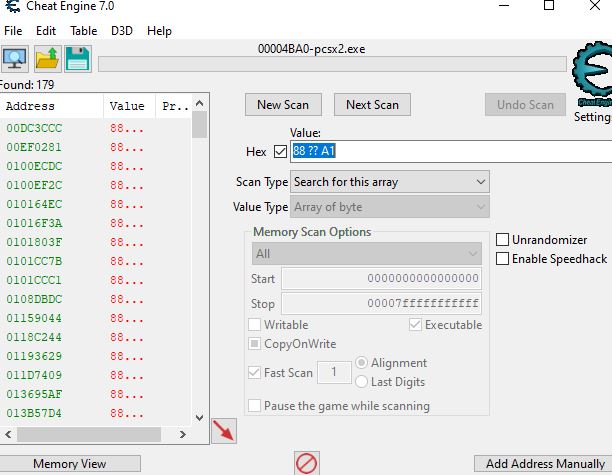
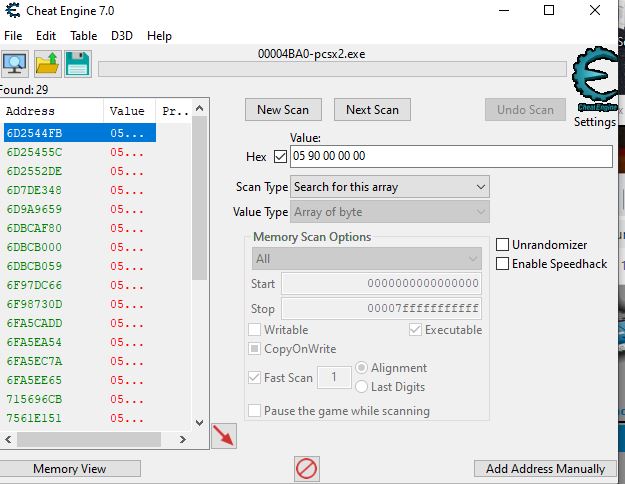
In the main window, set the scan type to array of bytes, clear the writable checkbox, check the executable checkbox, grey the CoW checkbox, scan for "88 11 A1", and for all the results in the exe, do to that address in the disassembler and check to see if it looks like it could be the injection point ("find out what addresses this instruction accesses" on "mov [ecx],dl"). If that fails, try "88 ?? A1". Scanning for "05 90 00 00 00" and scrolling up a bit in the disassembler might work too.
_________________
I don't know where I'm going, but I'll figure it out when I get there. |
|
| Back to top |
|
 |
Mystic974
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 27 May 2020
Posts: 8
|
 Posted: Fri May 29, 2020 10:02 am Post subject: Posted: Fri May 29, 2020 10:02 am Post subject: |
 |
|
| ParkourPenguin wrote: |
Scanning for fewer bytes of the original injection point might work, but you don't have much to go on.
In the main window, set the scan type to array of bytes, clear the writable checkbox, check the executable checkbox, grey the CoW checkbox, scan for "88 11 A1", and for all the results in the exe, do to that address in the disassembler and check to see if it looks like it could be the injection point ("find out what addresses this instruction accesses" on "mov [ecx],dl"). If that fails, try "88 ?? A1". Scanning for "05 90 00 00 00" and scrolling up a bit in the disassembler might work too. |
Thanks a lot for the help ! What should I do from the last screenshot?
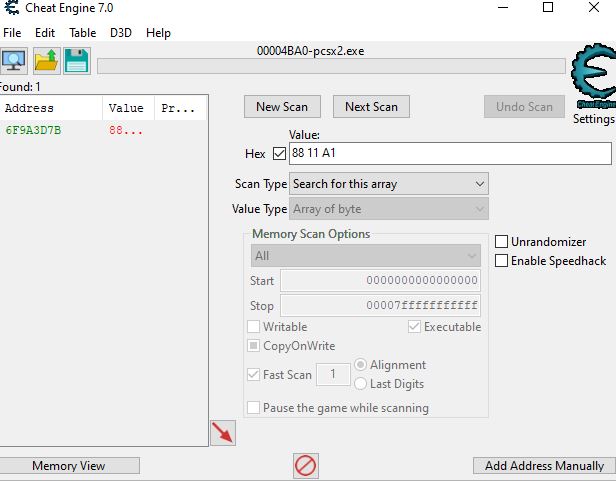
| Description: |
| I found this adress with the Shearch for this array shearch mod |
|
| Filesize: |
45.1 KB |
| Viewed: |
3214 Time(s) |
|
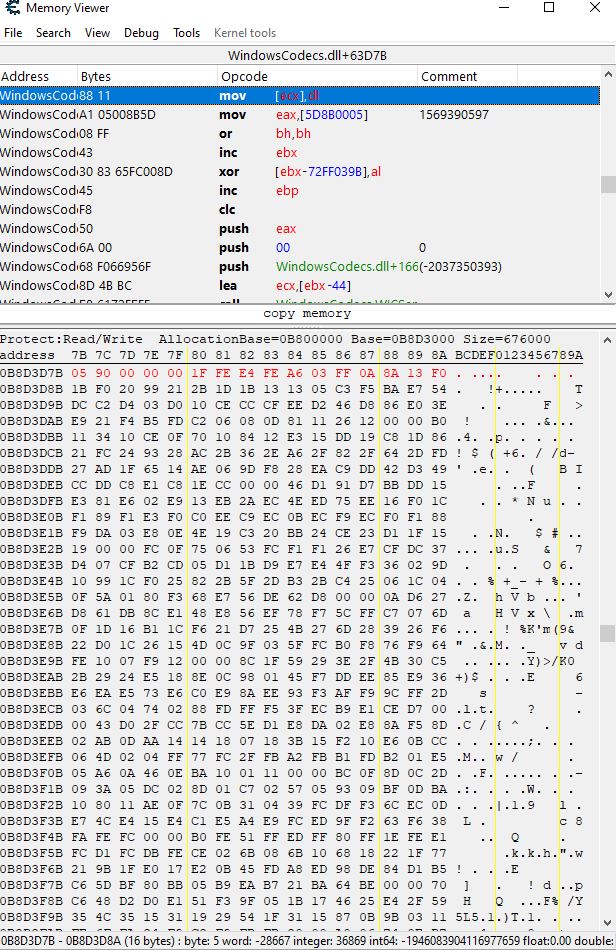
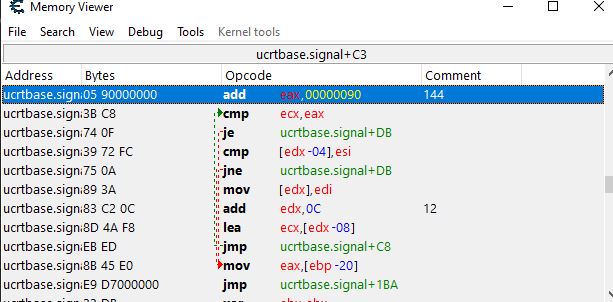
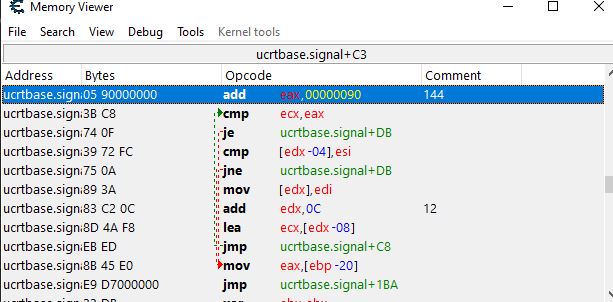
| Description: |
| I found this when scanning for 05 90 00 00 00 in the disassembler of the adress that I've found on the screenshot above. I've enlighted the adress |
|
| Filesize: |
187.11 KB |
| Viewed: |
3214 Time(s) |
|
|
|
| Back to top |
|
 |
ParkourPenguin
I post too much
 Reputation: 140 Reputation: 140
Joined: 06 Jul 2014
Posts: 4289
|
 Posted: Fri May 29, 2020 11:20 am Post subject: Posted: Fri May 29, 2020 11:20 am Post subject: |
 |
|
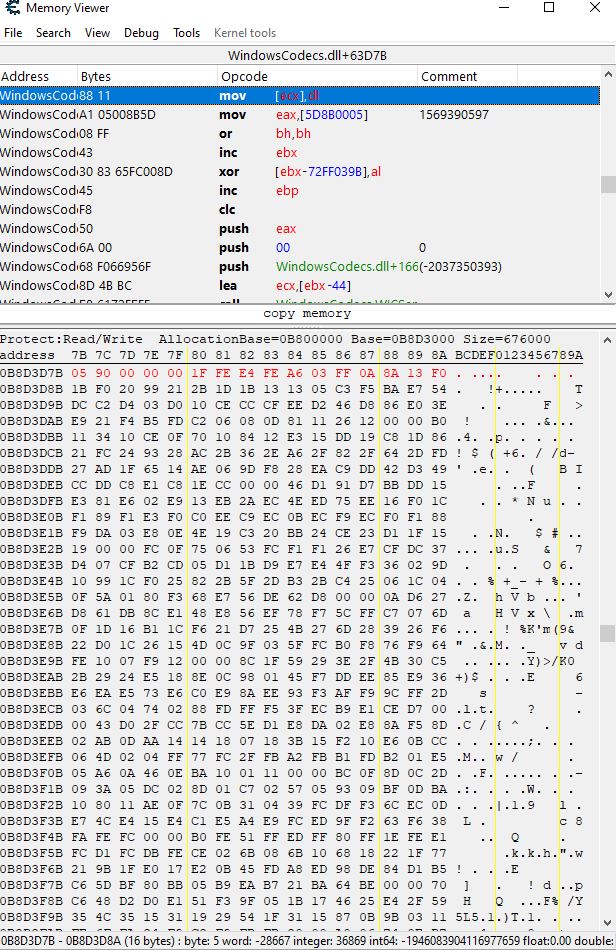
That's in WindowsCodes.dll, not pcsx2.exe. I strongly doubt that's the correct injection point.
Try "88 ?? A1", or try "05 90 00 00 00" and scroll up a bit in the disassembler.
_________________
I don't know where I'm going, but I'll figure it out when I get there. |
|
| Back to top |
|
 |
Mystic974
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 27 May 2020
Posts: 8
|
 Posted: Fri May 29, 2020 11:31 am Post subject: Posted: Fri May 29, 2020 11:31 am Post subject: |
 |
|
| ParkourPenguin wrote: | That's in WindowsCodes.dll, not pcsx2.exe. I strongly doubt that's the correct injection point.
Try "88 ?? A1", or try "05 90 00 00 00" and scroll up a bit in the disassembler. |
Do I have to do the same process for these shearchs?
If yes ,there is what I found :
| Description: |
|
| Filesize: |
56.85 KB |
| Viewed: |
3188 Time(s) |
|
| Description: |
|
| Filesize: |
60.18 KB |
| Viewed: |
3188 Time(s) |
|
Last edited by Mystic974 on Fri May 29, 2020 1:02 pm; edited 1 time in total |
|
| Back to top |
|
 |
ParkourPenguin
I post too much
 Reputation: 140 Reputation: 140
Joined: 06 Jul 2014
Posts: 4289
|
 Posted: Fri May 29, 2020 12:31 pm Post subject: Posted: Fri May 29, 2020 12:31 pm Post subject: |
 |
|
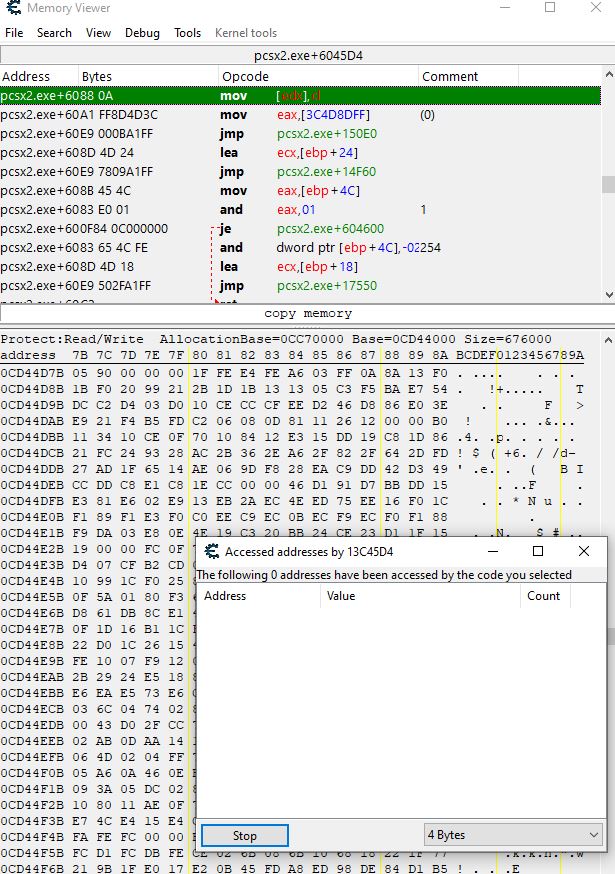
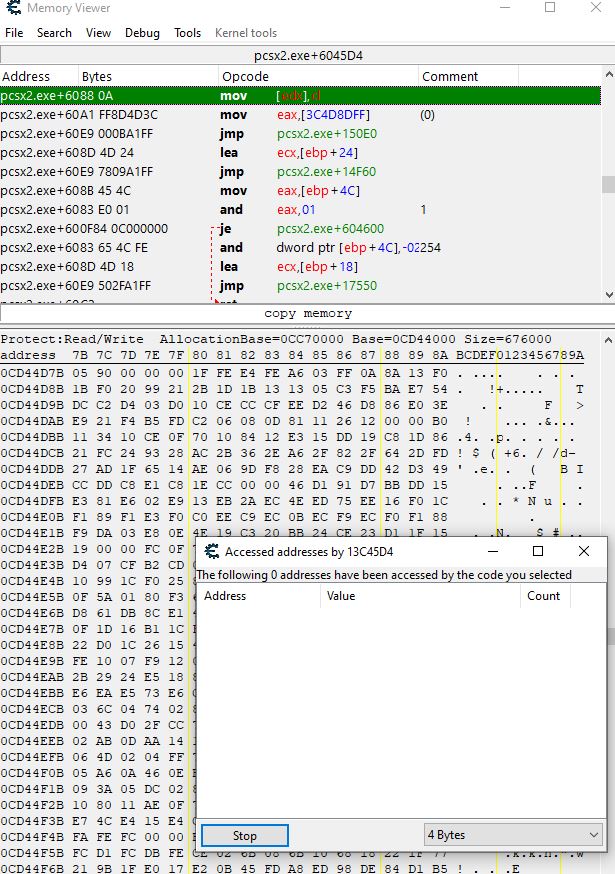
For all the addresses in the exe (they'll all be about in the same region), go through each one and check:
- That instruction is of the form "mov [e??],??"
- Those bytes are aligned to an instruction - scroll up a bit in the disassembler then scroll back down. If the instruction disappears, those bytes probably weren't aligned
- Right click the "mov [e??],??" instruction and select "Find out what addresses this instruction accesses". If the address you're looking for pops up, that's probably the original injection point.
Remember to first scroll up a bit for the "05 90 00 00 00" pattern.
If you still can't find it, you probably aren't ever going to. Instead, try to find that 0-255 byte value and check what writes to it. I don't know how you'd find that value- you'd need to figure that out.
_________________
I don't know where I'm going, but I'll figure it out when I get there. |
|
| Back to top |
|
 |
Mystic974
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 27 May 2020
Posts: 8
|
 Posted: Fri May 29, 2020 2:08 pm Post subject: Posted: Fri May 29, 2020 2:08 pm Post subject: |
 |
|
| ParkourPenguin wrote: | For all the addresses in the exe (they'll all be about in the same region), go through each one and check:
- That instruction is of the form "mov [e??],??"
- Those bytes are aligned to an instruction - scroll up a bit in the disassembler then scroll back down. If the instruction disappears, those bytes probably weren't aligned
- Right click the "mov [e??],??" instruction and select "Find out what addresses this instruction accesses". If the address you're looking for pops up, that's probably the original injection point.
Remember to first scroll up a bit for the "05 90 00 00 00" pattern. |
Here is all of the adresses with 88 ?? A1 for mov [e??],?? that I've found,but 0 of them accesses to any adress.
pcsx2.exe+24ECDC - 88 06 - mov [esi],al
pcsx2.exe+6019D4 - 88 36 - mov [esi],dh
pcsx2.exe+6044D4 - 88 0B - mov [ebx],cl
pcsx2.exe+6045D4 - 88 0A - mov [edx],cl
pcsx2.exe+64D204 - 88 06 - mov [esi],al
They all have the 05 90 00 00 00 pattern (I used scan memory/array of byte : 05 90 00 00 00 to find it in the disassembler)
I've found way more of that like "DSOUND.dll+29954 - 88 36 - mov [esi],dh"and many other different types but I doubt it's usefull.Also they don't access to any adresses too.
| ParkourPenguin wrote: | | If you still can't find it, you probably aren't ever going to. Instead, try to find that 0-255 byte value and check what writes to it. I don't know how you'd find that value- you'd need to figure that out. |
I will try that. Oh my...It's gonna be hard x) And thank you very much for all your help !
| Description: |
| Shearch result with 05 90 00 00 00,same "add" result for all of them |
|
| Filesize: |
49.24 KB |
| Viewed: |
3139 Time(s) |
|
| Description: |
| Here is what I got for all the mov [e??],?? that I've found with 88 ?? A1 |
|
| Filesize: |
145.54 KB |
| Viewed: |
3139 Time(s) |
|
|
|
| Back to top |
|
 |
ParkourPenguin
I post too much
 Reputation: 140 Reputation: 140
Joined: 06 Jul 2014
Posts: 4289
|
 Posted: Fri May 29, 2020 7:17 pm Post subject: Posted: Fri May 29, 2020 7:17 pm Post subject: |
 |
|
You might need to do some action in the game in order for code to run and have something come up in the "accessed addresses" window. I'm not sure what that action would be... opening a menu? Perhaps when bodyguards spawn?
Narrowing it down to only 5 is good. You could set a breakpoint at each of them (highlight instruction, Debug -> Set breakpoint), play the game for a while, and if it suddenly stops working, go to CE and see what instruction triggered the breakpoint. If a breakpoint triggers too often and it's never what you're looking for, remove the breakpoint- it's probably not the correct instruction.
Or watch the accessed addresses of all 5, but you'd need to remember to check if anything comes up while playing.
_________________
I don't know where I'm going, but I'll figure it out when I get there. |
|
| Back to top |
|
 |
|

 Reputation: 32
Reputation: 32 Reputation: 140
Reputation: 140 Reputation: 198
Reputation: 198 Reputation: 140
Reputation: 140 Reputation: 140
Reputation: 140 Reputation: 140
Reputation: 140 Reputation: 140
Reputation: 140