|
Cheat Engine The Official Site of Cheat Engine |
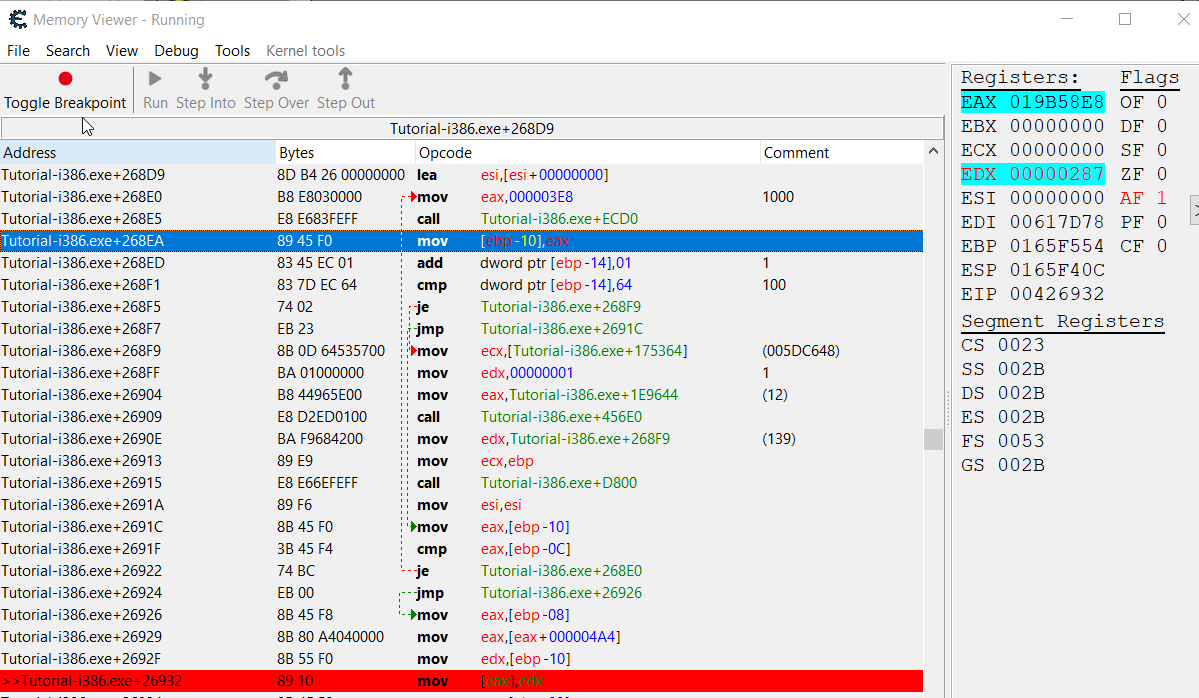
| Understanding instructions from disassembler |
| Author | Message | ||||||
|---|---|---|---|---|---|---|---|
| DreamingJ How do I cheat? Joined: 22 Jan 2020 Posts: 3 |
|||||||
| ParkourPenguin I post too much  Reputation: 154 Reputation: 154Joined: 06 Jul 2014 Posts: 4749 |
|
||||||
| All times are GMT - 6 Hours |
||
|
You cannot post new topics in this forum You cannot reply to topics in this forum You cannot edit your posts in this forum You cannot delete your posts in this forum You cannot vote in polls in this forum You cannot attach files in this forum You can download files in this forum |
Powered by phpBB © 2001, 2005 phpBB Group
CE Wiki IRC (#CEF) Twitter
Third party websites