| View previous topic :: View next topic |
| Author |
Message |
Rotschild
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 23 Jul 2012
Posts: 11
|
 Posted: Fri Nov 08, 2019 7:33 pm Post subject: Bluestacks AOB Alloc pointer problem Posted: Fri Nov 08, 2019 7:33 pm Post subject: Bluestacks AOB Alloc pointer problem |
 |
|
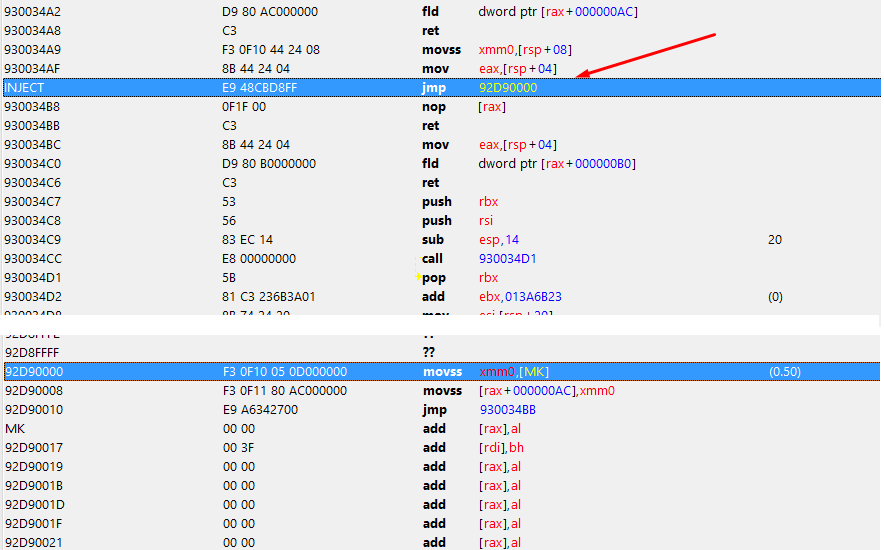
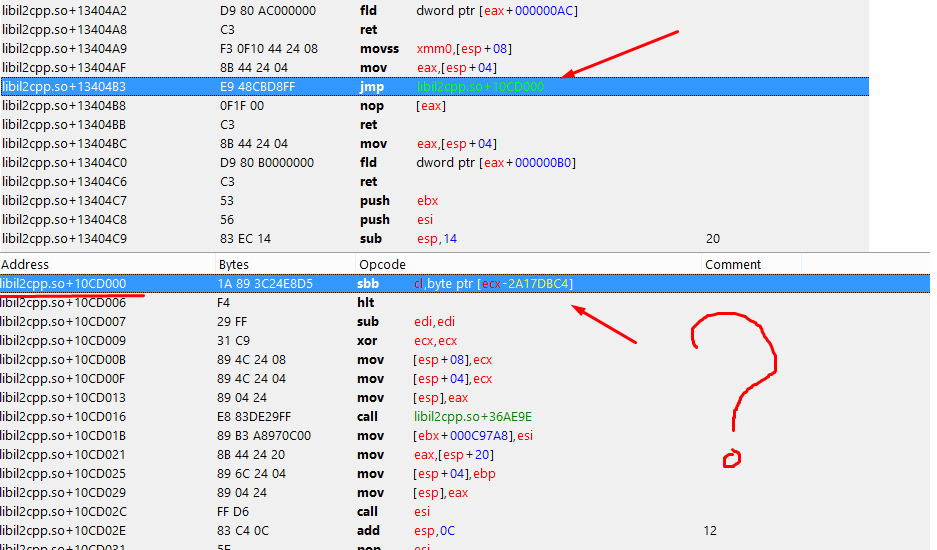
I have problem with AOB AutoAssable with BlueStacks memory.
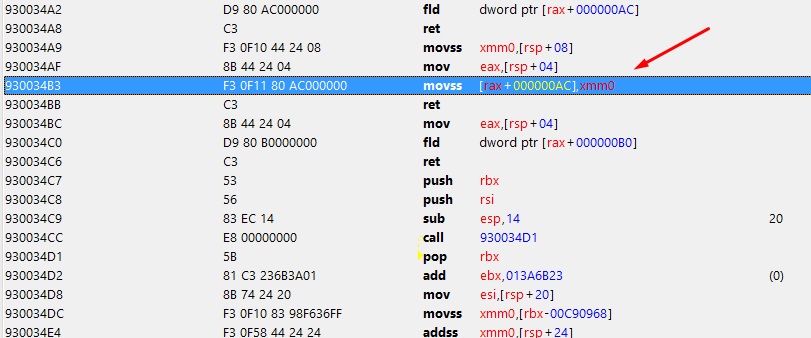
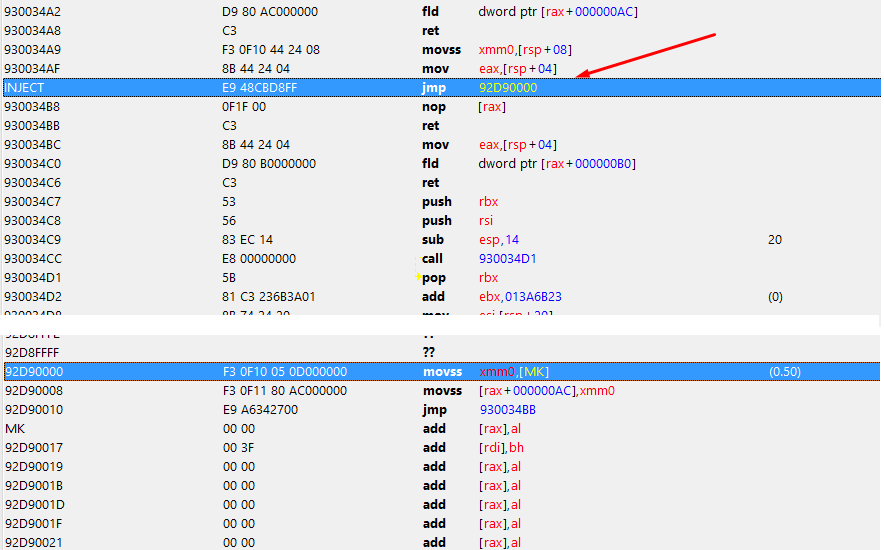
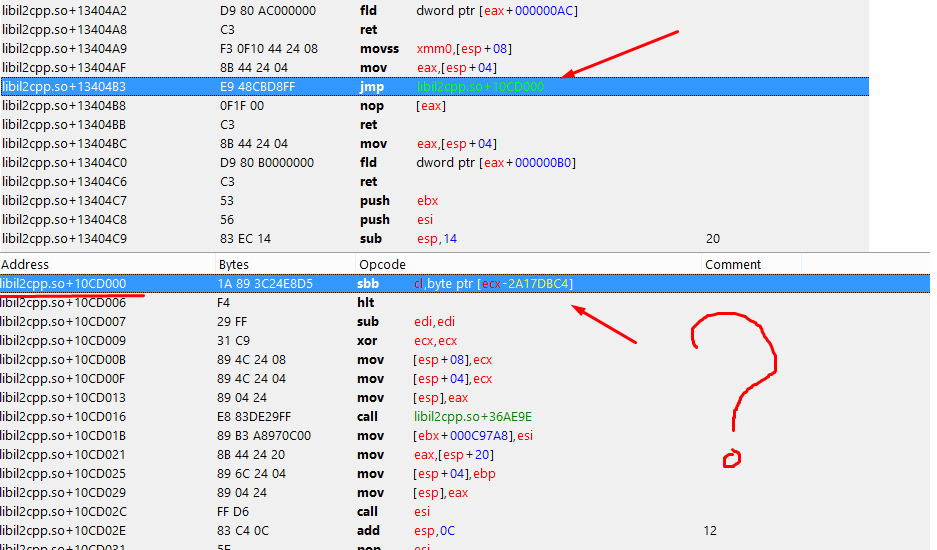
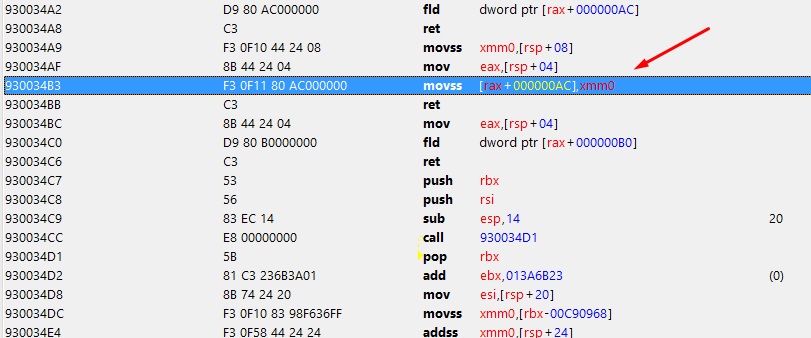
I want to create Jump for new memory region created by AOB script (pic1) and it works fine in CT MemoryViewer that is outside BlueStacks (Pic2) but when i look at what have script done in CT MemoryViewer from inside BlueStacks (ceserver_x86) i see some crazy jump to nowhere(Pic3). And as a result - app crash.
I assume this is Alloc problems. BlueStacks has its own virtual address table inside itself. How can i fix it?
| Description: |
|
| Filesize: |
83.57 KB |
| Viewed: |
6500 Time(s) |
|
| Description: |
|
| Filesize: |
33.98 KB |
| Viewed: |
6500 Time(s) |
|
| Description: |
|
| Filesize: |
46.47 KB |
| Viewed: |
6500 Time(s) |
|
|
|
| Back to top |
|
 |
Dark Byte
Site Admin
 Reputation: 458 Reputation: 458
Joined: 09 May 2003
Posts: 25287
Location: The netherlands
|
 Posted: Sat Nov 09, 2019 1:06 am Post subject: Posted: Sat Nov 09, 2019 1:06 am Post subject: |
 |
|
From outside bluestacks you are working on the physical memory ofbthe android device, not on the virtual memory of the process running inside the android device.
You need to do the alloc from inside ceserver. Which will require the extension module te get injected into the target first (sometimes the inject works fine, but i never tested that on bluestacks)
Then do the jmp from inside ceserver as well, else the jump distance is wrong, as virtual memory is randomized over physical memory in 4096 byte blocks
-
else find a codecave inside the target process and use and aob to find that.
Then build the jmp yourself using the virtual address of origin and destination
_________________
Do not ask me about online cheats. I don't know any and wont help finding them.
Like my help? Join me on Patreon so i can keep helping |
|
| Back to top |
|
 |
Doraneko
Newbie cheater
![]() Reputation: 1 Reputation: 1
Joined: 22 Jul 2018
Posts: 10
Location: Japan Tokyo
|
 Posted: Sat Nov 09, 2019 3:13 pm Post subject: Posted: Sat Nov 09, 2019 3:13 pm Post subject: |
 |
|
ceserver's so injection is a little unstable.
Load libceserver-extension_x86.so directly embedded in apk (like frida-gadget).
Or you can inject the so file with frida.
I have confirmed that CE AutoAssemble works correctly with NoxAppPlayer using the above method.
|
|
| Back to top |
|
 |
nadinemagazine
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 09 Nov 2019
Posts: 0
|
 Posted: Sat Nov 09, 2019 3:18 pm Post subject: thank you Posted: Sat Nov 09, 2019 3:18 pm Post subject: thank you |
 |
|
thanks
_________________
Rawshna. |
|
| Back to top |
|
 |
Rotschild
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 23 Jul 2012
Posts: 11
|
 Posted: Wed Nov 13, 2019 10:32 pm Post subject: Posted: Wed Nov 13, 2019 10:32 pm Post subject: |
 |
|
| Dark Byte wrote: | From outside bluestacks you are working on the physical memory ofbthe android device, not on the virtual memory of the process running inside the android device.
You need to do the alloc from inside ceserver. Which will require the extension module te get injected into the target first (sometimes the inject works fine, but i never tested that on bluestacks)
Then do the jmp from inside ceserver as well, else the jump distance is wrong, as virtual memory is randomized over physical memory in 4096 byte blocks
-
else find a codecave inside the target process and use and aob to find that.
Then build the jmp yourself using the virtual address of origin and destination |
Actually cesrver extension injection is not working on Bluestacks and even on Nox.
Unfortunately, there is no codecaves 4kb near in my target code. I think i will Ret some unused nearby function and will use flesh of this function as donor.
| Doraneko wrote: | ceserver's so injection is a little unstable.
Load libceserver-extension_x86.so directly embedded in apk (like frida-gadget).
Or you can inject the so file with frida.
I have confirmed that CE AutoAssemble works correctly with NoxAppPlayer using the above method. |
Installing Frida was really pain in the ass.
How do you inject .so library with Frida? There is no frida-inject in windows-python-pip version. Only frida, frida-trace, frida-ps.
Interesting application. But for some reason, "frida-trace -U -f MYAPP -i SSLRead" doesn't give me any results (no handler was generated). Its a pity (( I tried for years to see what is sending in SSL traffic on Android(with no cert pinning bypass).
|
|
| Back to top |
|
 |
Doraneko
Newbie cheater
![]() Reputation: 1 Reputation: 1
Joined: 22 Jul 2018
Posts: 10
Location: Japan Tokyo
|
 Posted: Fri Nov 15, 2019 8:45 am Post subject: Posted: Fri Nov 15, 2019 8:45 am Post subject: |
 |
|
I verified with a common so file injection program.
(x86 program => x86 program)
Nox 4.4.2: Failure
Nox 5.1.1: Success
Nox 7.1.2: Failure
(x86 program => ARM program)
In the above case, an emulator hooking library called 「EHook」 is used.
I also succeeded with Nox 5.1.1 by modifying the ceserver program. But I didn't know why this was successful.
In Frida, if you implement a script that invokes dlopen, it is possible in Nox5.1.1.
|
|
| Back to top |
|
 |
Rotschild
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 23 Jul 2012
Posts: 11
|
 Posted: Fri Nov 15, 2019 3:59 pm Post subject: Posted: Fri Nov 15, 2019 3:59 pm Post subject: |
 |
|
| Doraneko wrote: | I verified with a common so file injection program.
(x86 program => x86 program)
Nox 4.4.2: Failure
Nox 5.1.1: Success
Nox 7.1.2: Failure
(x86 program => ARM program)
In the above case, an emulator hooking library called 「EHook」 is used.
I also succeeded with Nox 5.1.1 by modifying the ceserver program. But I didn't know why this was successful.
In Frida, if you implement a script that invokes dlopen, it is possible in Nox5.1.1. |
I thought there were easier and more stable ways 
Whatever thanks.
|
|
| Back to top |
|
 |
|

 Reputation: 458
Reputation: 458