|
Cheat Engine
The Official Site of Cheat Engine
|
| View previous topic :: View next topic |
| Author |
Message |
dharmang1910
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 09 May 2010
Posts: 102
|
 Posted: Sat Dec 08, 2018 12:41 am Post subject: Game crash at popfd Posted: Sat Dec 08, 2018 12:41 am Post subject: Game crash at popfd |
 |
|
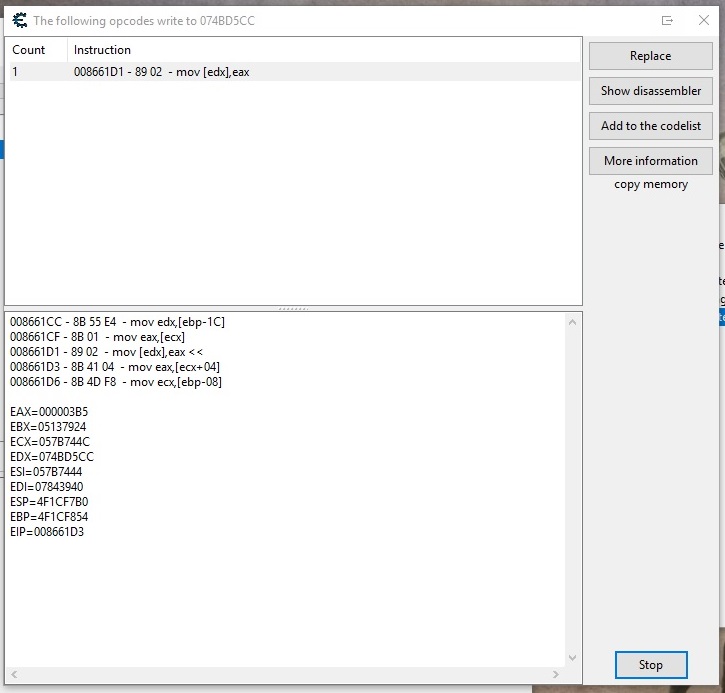
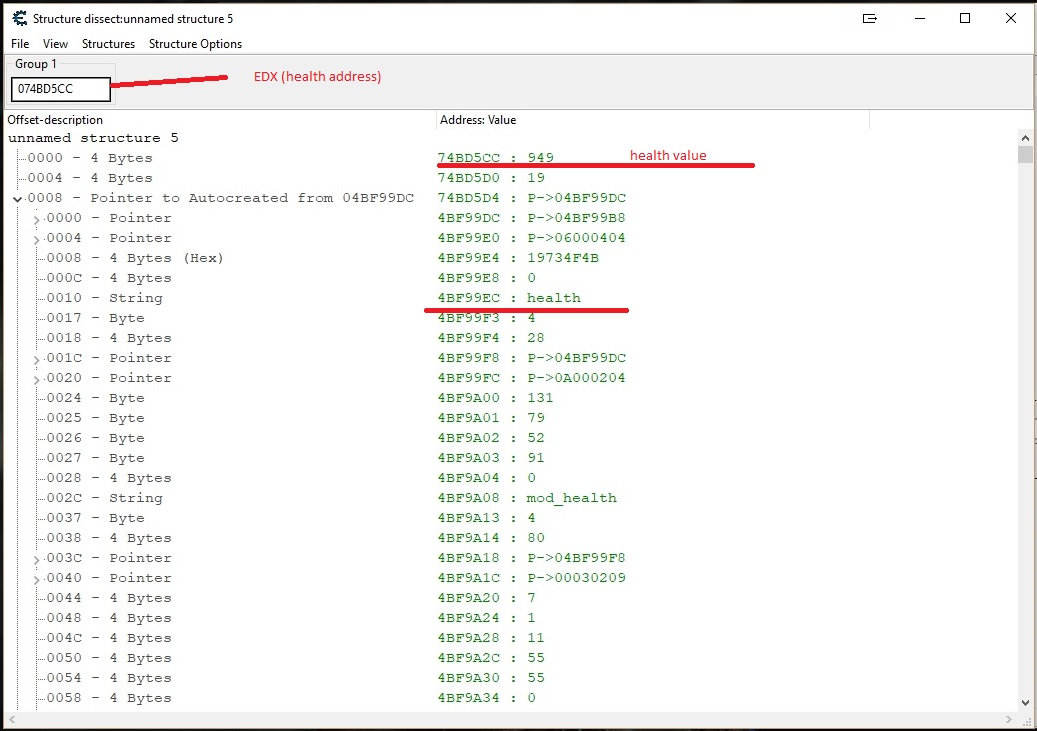
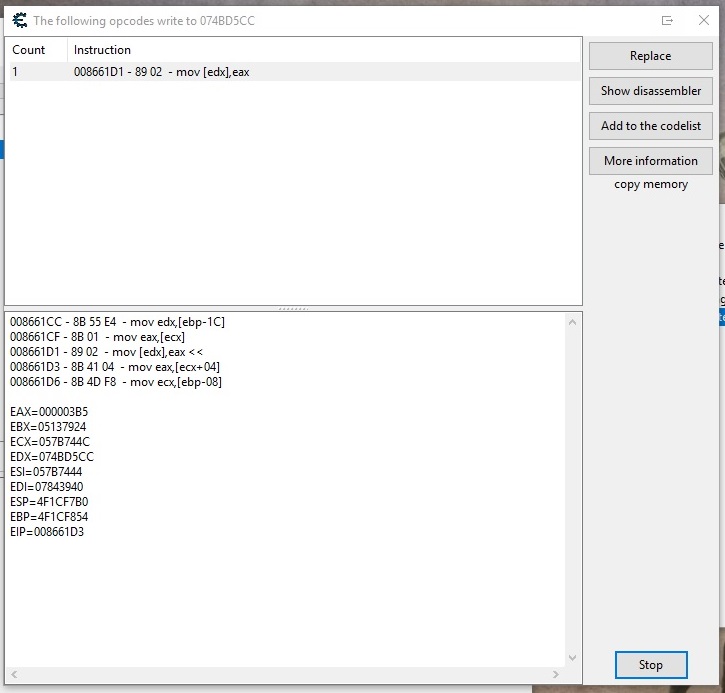
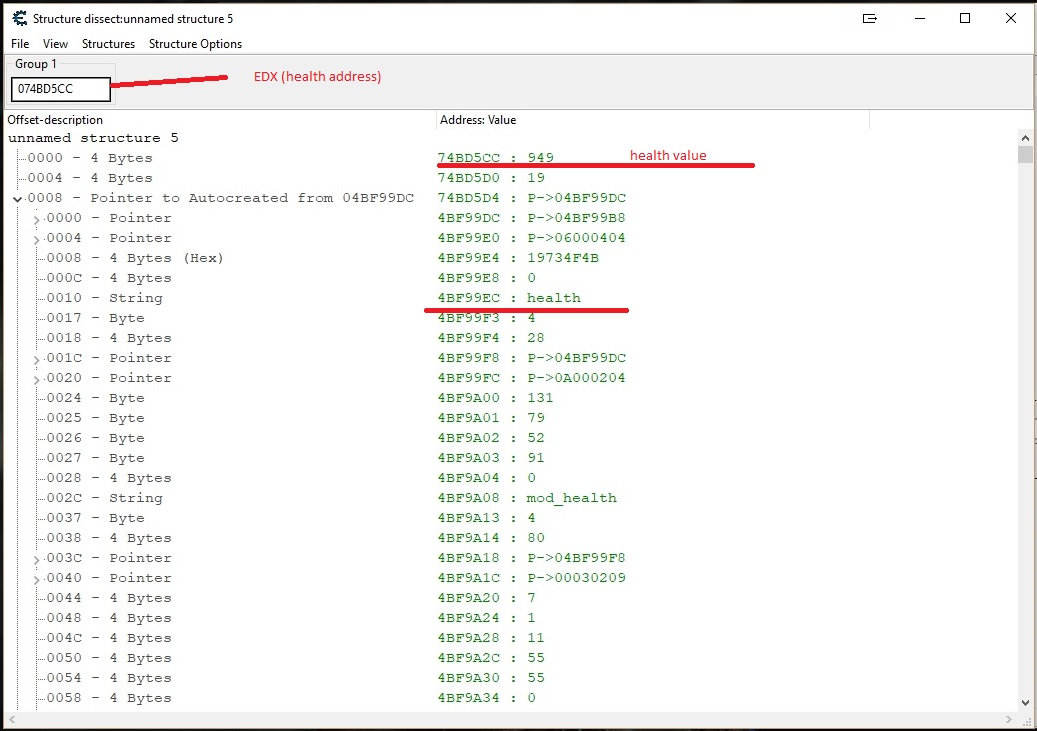
I am making table for victor vran game. This is lua game and heath address is writing through a shared opcode which accessing lots of addresses. So i have made a script as below:
| Code: | [ENABLE]
aobscanmodule(health,VictorVranSteam.exe,89 02 8B 41 04 8B 4D F8) // should be unique
alloc(newmem,$1000)
label(code)
label(return)
label(park)
newmem:
pushfd
pushad
//--------------check edx+8 is valid pointer
lea eax,[edx+8]
push 00000004
push eax
call isbadreadptr
cmp eax,0
jne park //not valid poiner then go to park otherwise continue
//----------------------check health string
lea eax,[edx+8]
cmp dword ptr[eax+10],'heal'
jne park
cmp dword ptr[eax+14],'th'
jne park
//-----------if health string then write health
mov eax,3e8
jmp code
park:
popfd
popad
jmp code
code:
mov [edx],eax
mov eax,[ecx+04]
jmp return
health:
jmp newmem
return:
registersymbol(health)
[DISABLE]
health:
db 89 02 8B 41 04
unregistersymbol(health)
dealloc(newmem)
{
// ORIGINAL CODE - INJECTION POINT: "VictorVranSteam.exe"+4661D1
"VictorVranSteam.exe"+4661B7: 8B 01 - mov eax,[ecx]
"VictorVranSteam.exe"+4661B9: F6 40 05 03 - test byte ptr [eax+05],03
"VictorVranSteam.exe"+4661BD: 74 10 - je VictorVranSteam.exe+4661CF
"VictorVranSteam.exe"+4661BF: 56 - push esi
"VictorVranSteam.exe"+4661C0: 57 - push edi
"VictorVranSteam.exe"+4661C1: E8 CA E8 FE FF - call VictorVranSteam.exe+454A90
"VictorVranSteam.exe"+4661C6: 8B 4D FC - mov ecx,[ebp-04]
"VictorVranSteam.exe"+4661C9: 83 C4 08 - add esp,08
"VictorVranSteam.exe"+4661CC: 8B 55 E4 - mov edx,[ebp-1C]
"VictorVranSteam.exe"+4661CF: 8B 01 - mov eax,[ecx]
// ---------- INJECTING HERE ----------
"VictorVranSteam.exe"+4661D1: 89 02 - mov [edx],eax
"VictorVranSteam.exe"+4661D3: 8B 41 04 - mov eax,[ecx+04]
// ---------- DONE INJECTING ----------
"VictorVranSteam.exe"+4661D6: 8B 4D F8 - mov ecx,[ebp-08]
"VictorVranSteam.exe"+4661D9: 89 42 04 - mov [edx+04],eax
"VictorVranSteam.exe"+4661DC: E9 BF FB FF FF - jmp VictorVranSteam.exe+465DA0
"VictorVranSteam.exe"+4661E1: 8B 7D 08 - mov edi,[ebp+08]
"VictorVranSteam.exe"+4661E4: 8B C2 - mov eax,edx
"VictorVranSteam.exe"+4661E6: C1 EA 0E - shr edx,0E
"VictorVranSteam.exe"+4661E9: C1 E8 17 - shr eax,17
"VictorVranSteam.exe"+4661EC: 81 E2 FF 01 00 00 - and edx,000001FF
"VictorVranSteam.exe"+4661F2: 57 - push edi
"VictorVranSteam.exe"+4661F3: 89 45 FC - mov [ebp-04],eax
} |
but game crash when i activate this script. I have made breakpoint at beginning of this script and game crash when reach at popfd instruction. I don't know is there any mistakes in script or there is other problem. can anybody give me any suggestion.
| Description: |
|
| Filesize: |
68.07 KB |
| Viewed: |
12251 Time(s) |
|
| Description: |
|
| Filesize: |
141.07 KB |
| Viewed: |
12251 Time(s) |
|
|
|
| Back to top |
|
 |
atom0s
Moderator
 Reputation: 198 Reputation: 198
Joined: 25 Jan 2006
Posts: 8517
Location: 127.0.0.1
|
 Posted: Sat Dec 08, 2018 2:24 am Post subject: Posted: Sat Dec 08, 2018 2:24 am Post subject: |
 |
|
You are pushing things onto the stack but in certain conditions never removing them. Your last bit:
| Code: | //-----------if health string then write health
mov eax,3e8
jmp code |
Skips over the popfd/popad which is going to crash due to an unbalanced stack.
_________________
- Retired. |
|
| Back to top |
|
 |
dharmang1910
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 09 May 2010
Posts: 102
|
 Posted: Sat Dec 08, 2018 3:42 am Post subject: Posted: Sat Dec 08, 2018 3:42 am Post subject: |
 |
|
| atom0s wrote: | You are pushing things onto the stack but in certain conditions never removing them. Your last bit:
| Code: | //-----------if health string then write health
mov eax,3e8
jmp code |
Skips over the popfd/popad which is going to crash due to an unbalanced stack. |
This thing not works
| Code: | //-----------if health string then write health
add esp,8
mov eax,3e8
jmp code |
i have removed pushfd/popfd but not pushad/popad and game is not crashing but it can accesses multiple address that don't have "health" string. Can i doing something wrong?
|
|
| Back to top |
|
 |
OldCheatEngineUser
Whateven rank
 Reputation: 20 Reputation: 20
Joined: 01 Feb 2016
Posts: 1587
|
 Posted: Sat Dec 08, 2018 4:58 am Post subject: Posted: Sat Dec 08, 2018 4:58 am Post subject: |
 |
|
| Code: | [ENABLE]
aobscanmodule(health,VictorVranSteam.exe,89 02 8B 41 04 8B 4D F8) // should be unique
alloc(newmem,$1000)
label(code)
label(return)
label(park)
newmem:
pushfd
pushad
//--------------check edx+8 is valid pointer
lea eax,[edx+8]
push 00000004
push eax
call isbadreadptr
cmp eax,0
popad // because of x86 calling conventions
jne park //not valid poiner then go to park otherwise continue
//----------------------check health string
lea eax,[edx+8]
cmp dword ptr[eax+10],'heal'
jne park
// cmp dword ptr[eax+14],'th' // you are comparing 4 bytes after [eax+14]
cmp word ptr [eax+14],'th' // while you only need to compare 2 bytes
// so use WORD instead of DWORD
jne park
//-----------if health string then write health
mov eax,3e8
// jmp code // you dont need it unless you will add more code here
// you have to pop the flags from the stack, thats why i removed the "jmp code"
// so after "mov eax,3e8" popfd will be executed then the originalcode
park:
popfd
// popad you dont need it
// jmp code // you dont need it
code:
mov [edx],eax
mov eax,[ecx+04]
jmp return
health:
jmp newmem
return:
registersymbol(health)
[DISABLE]
health:
db 89 02 8B 41 04
unregistersymbol(health)
dealloc(newmem)
{
// ORIGINAL CODE - INJECTION POINT: "VictorVranSteam.exe"+4661D1
"VictorVranSteam.exe"+4661B7: 8B 01 - mov eax,[ecx]
"VictorVranSteam.exe"+4661B9: F6 40 05 03 - test byte ptr [eax+05],03
"VictorVranSteam.exe"+4661BD: 74 10 - je VictorVranSteam.exe+4661CF
"VictorVranSteam.exe"+4661BF: 56 - push esi
"VictorVranSteam.exe"+4661C0: 57 - push edi
"VictorVranSteam.exe"+4661C1: E8 CA E8 FE FF - call VictorVranSteam.exe+454A90
"VictorVranSteam.exe"+4661C6: 8B 4D FC - mov ecx,[ebp-04]
"VictorVranSteam.exe"+4661C9: 83 C4 08 - add esp,08
"VictorVranSteam.exe"+4661CC: 8B 55 E4 - mov edx,[ebp-1C]
"VictorVranSteam.exe"+4661CF: 8B 01 - mov eax,[ecx]
// ---------- INJECTING HERE ----------
"VictorVranSteam.exe"+4661D1: 89 02 - mov [edx],eax
"VictorVranSteam.exe"+4661D3: 8B 41 04 - mov eax,[ecx+04]
// ---------- DONE INJECTING ----------
"VictorVranSteam.exe"+4661D6: 8B 4D F8 - mov ecx,[ebp-08]
"VictorVranSteam.exe"+4661D9: 89 42 04 - mov [edx+04],eax
"VictorVranSteam.exe"+4661DC: E9 BF FB FF FF - jmp VictorVranSteam.exe+465DA0
"VictorVranSteam.exe"+4661E1: 8B 7D 08 - mov edi,[ebp+08]
"VictorVranSteam.exe"+4661E4: 8B C2 - mov eax,edx
"VictorVranSteam.exe"+4661E6: C1 EA 0E - shr edx,0E
"VictorVranSteam.exe"+4661E9: C1 E8 17 - shr eax,17
"VictorVranSteam.exe"+4661EC: 81 E2 FF 01 00 00 - and edx,000001FF
"VictorVranSteam.exe"+4661F2: 57 - push edi
"VictorVranSteam.exe"+4661F3: 89 45 FC - mov [ebp-04],eax
} |
_________________
About Me;
I Use CE Since Version 1.X, And Still Learning How To Use It Well!
Jul 26, 2020
| STN wrote: | | i am a sweetheart. |
|
|
| Back to top |
|
 |
dharmang1910
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 09 May 2010
Posts: 102
|
 Posted: Sat Dec 08, 2018 5:59 am Post subject: Posted: Sat Dec 08, 2018 5:59 am Post subject: |
 |
|
| OldCheatEngineUser wrote: | | Code: | [ENABLE]
aobscanmodule(health,VictorVranSteam.exe,89 02 8B 41 04 8B 4D F8) // should be unique
alloc(newmem,$1000)
label(code)
label(return)
label(park)
newmem:
pushfd
pushad
//--------------check edx+8 is valid pointer
lea eax,[edx+8]
push 00000004
push eax
call isbadreadptr
cmp eax,0
popad // because of x86 calling conventions
jne park //not valid poiner then go to park otherwise continue
//----------------------check health string
lea eax,[edx+8]
cmp dword ptr[eax+10],'heal'
jne park
// cmp dword ptr[eax+14],'th' // you are comparing 4 bytes after [eax+14]
cmp word ptr [eax+14],'th' // while you only need to compare 2 bytes
// so use WORD instead of DWORD
jne park
//-----------if health string then write health
mov eax,3e8
// jmp code // you dont need it unless you will add more code here
// you have to pop the flags from the stack, thats why i removed the "jmp code"
// so after "mov eax,3e8" popfd will be executed then the originalcode
park:
popfd
// popad you dont need it
// jmp code // you dont need it
code:
mov [edx],eax
mov eax,[ecx+04]
jmp return
health:
jmp newmem
return:
registersymbol(health)
[DISABLE]
health:
db 89 02 8B 41 04
unregistersymbol(health)
dealloc(newmem)
{
// ORIGINAL CODE - INJECTION POINT: "VictorVranSteam.exe"+4661D1
"VictorVranSteam.exe"+4661B7: 8B 01 - mov eax,[ecx]
"VictorVranSteam.exe"+4661B9: F6 40 05 03 - test byte ptr [eax+05],03
"VictorVranSteam.exe"+4661BD: 74 10 - je VictorVranSteam.exe+4661CF
"VictorVranSteam.exe"+4661BF: 56 - push esi
"VictorVranSteam.exe"+4661C0: 57 - push edi
"VictorVranSteam.exe"+4661C1: E8 CA E8 FE FF - call VictorVranSteam.exe+454A90
"VictorVranSteam.exe"+4661C6: 8B 4D FC - mov ecx,[ebp-04]
"VictorVranSteam.exe"+4661C9: 83 C4 08 - add esp,08
"VictorVranSteam.exe"+4661CC: 8B 55 E4 - mov edx,[ebp-1C]
"VictorVranSteam.exe"+4661CF: 8B 01 - mov eax,[ecx]
// ---------- INJECTING HERE ----------
"VictorVranSteam.exe"+4661D1: 89 02 - mov [edx],eax
"VictorVranSteam.exe"+4661D3: 8B 41 04 - mov eax,[ecx+04]
// ---------- DONE INJECTING ----------
"VictorVranSteam.exe"+4661D6: 8B 4D F8 - mov ecx,[ebp-08]
"VictorVranSteam.exe"+4661D9: 89 42 04 - mov [edx+04],eax
"VictorVranSteam.exe"+4661DC: E9 BF FB FF FF - jmp VictorVranSteam.exe+465DA0
"VictorVranSteam.exe"+4661E1: 8B 7D 08 - mov edi,[ebp+08]
"VictorVranSteam.exe"+4661E4: 8B C2 - mov eax,edx
"VictorVranSteam.exe"+4661E6: C1 EA 0E - shr edx,0E
"VictorVranSteam.exe"+4661E9: C1 E8 17 - shr eax,17
"VictorVranSteam.exe"+4661EC: 81 E2 FF 01 00 00 - and edx,000001FF
"VictorVranSteam.exe"+4661F2: 57 - push edi
"VictorVranSteam.exe"+4661F3: 89 45 FC - mov [ebp-04],eax
} |
|
Thanks for your reply, but game is still crashing. I have made script like this, as you suggested game is not crashing but still it access non health string values and so no god mode.
| Code: | [ENABLE]
aobscanmodule(health,VictorVranSteam.exe,89 02 8B 41 04 8B 4D F8) // should be unique
alloc(newmem,$1000)
alloc(hlth,4)
registersymbol(hlth)
label(code)
label(return)
label(park)
newmem:
//pushfd
pushad
//--------------check edx+8 is valid pointer
lea eax,[edx+8]
push 00000004
push eax
call isbadreadptr
cmp eax,0
jne park //not valid poiner then go to park otherwise continue
//----------------------check health string
lea eax,[edx+8]
mov [hlth],eax
cmp dword ptr[eax+34],'heal'
jne park
cmp word ptr[eax+14],'th'
jne park
//-----------if health string then write health
add esp,8
mov eax,3e8
jmp code
park:
//popfd
popad
jmp code
code:
mov [edx],eax
mov eax,[ecx+04]
jmp return
health:
jmp newmem
return:
registersymbol(health)
[DISABLE]
health:
db 89 02 8B 41 04
unregistersymbol(health)
dealloc(newmem)
|
|
|
| Back to top |
|
 |
OldCheatEngineUser
Whateven rank
 Reputation: 20 Reputation: 20
Joined: 01 Feb 2016
Posts: 1587
|
 Posted: Sat Dec 08, 2018 6:33 am Post subject: Posted: Sat Dec 08, 2018 6:33 am Post subject: |
 |
|
i cant believe that my script caused a crash. (because the same logic is tested twice)
about multiple addresses:
ensure your enemies dont have a string called 'health'
_________________
About Me;
I Use CE Since Version 1.X, And Still Learning How To Use It Well!
Jul 26, 2020
| STN wrote: | | i am a sweetheart. |
|
|
| Back to top |
|
 |
dharmang1910
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 09 May 2010
Posts: 102
|
 Posted: Sat Dec 08, 2018 7:49 am Post subject: Posted: Sat Dec 08, 2018 7:49 am Post subject: |
 |
|
| OldCheatEngineUser wrote: | i cant believe that my script caused a crash. (because the same logic is tested twice)
about multiple addresses:
ensure your enemies dont have a string called 'health' |
yes i also can not understand what is going wrong, if enemy have also health string then player and enemy both have god mode but this game is crashing also when player are standing alone at safe place. I also want to inform you that this is lua game made with custom c++ game engine and it all of value are passed through this single code(when we are see what addresses are accessed by this code we are seen lots of values and also continuously adding new values).
|
|
| Back to top |
|
 |
OldCheatEngineUser
Whateven rank
 Reputation: 20 Reputation: 20
Joined: 01 Feb 2016
Posts: 1587
|
 Posted: Sat Dec 08, 2018 8:10 am Post subject: Posted: Sat Dec 08, 2018 8:10 am Post subject: |
 |
|
| dharmang1910 wrote: | | I also want to inform you that this is lua game made with custom c++ game engine and it all of value are passed through this single code(when we are see what addresses are accessed by this code we are seen lots of values and also continuously adding new values). |
ehm, this can cause lot of problems. (sounds like code emulation)
i cant really say a word without actual debugging, also i think the memory region that have the 'health' string is not static and get changed every now and then.
a simple method to get what you want is:
- find a pointer
- compare
- write
my script example
_________________
About Me;
I Use CE Since Version 1.X, And Still Learning How To Use It Well!
Jul 26, 2020
| STN wrote: | | i am a sweetheart. |
|
|
| Back to top |
|
 |
dharmang1910
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 09 May 2010
Posts: 102
|
 Posted: Sat Dec 08, 2018 8:51 am Post subject: Posted: Sat Dec 08, 2018 8:51 am Post subject: |
 |
|
| OldCheatEngineUser wrote: | | dharmang1910 wrote: | | I also want to inform you that this is lua game made with custom c++ game engine and it all of value are passed through this single code(when we are see what addresses are accessed by this code we are seen lots of values and also continuously adding new values). |
ehm, this can cause lot of problems. (sounds like code emulation)
i cant really say a word without actual debugging, also i think the memory region that have the 'health' string is not static and get changed every now and then.
a simple method to get what you want is:
- find a pointer
- compare
- write
my script example |
I have tried level 9 pointer but not works.
|
|
| Back to top |
|
 |
dharmang1910
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 09 May 2010
Posts: 102
|
 Posted: Sun Dec 09, 2018 2:25 am Post subject: Posted: Sun Dec 09, 2018 2:25 am Post subject: |
 |
|
| I have searched that eny have also health string but at +14 offset there is null pointer so that's way I have differentiate them but game is still crashing. On internet there is not a single table or trainer available for victor vran overkill edition. So this is the main reason why there is no cheats available. This game is impossible to hack.
|
|
| Back to top |
|
 |
Dark Byte
Site Admin
 Reputation: 458 Reputation: 458
Joined: 09 May 2003
Posts: 25287
Location: The netherlands
|
 Posted: Sun Dec 09, 2018 3:52 am Post subject: Posted: Sun Dec 09, 2018 3:52 am Post subject: |
 |
|
Perhaps {$try}/{$except} can help with the random crashes on memory access (Still be sure to keep the stack in a proper condition though)
https://wiki.cheatengine.org/index.php?title=Auto_Assembler:TRY_EXCEPT
_________________
Do not ask me about online cheats. I don't know any and wont help finding them.
Like my help? Join me on Patreon so i can keep helping |
|
| Back to top |
|
 |
dharmang1910
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 09 May 2010
Posts: 102
|
 Posted: Sun Dec 09, 2018 4:50 am Post subject: Posted: Sun Dec 09, 2018 4:50 am Post subject: |
 |
|
I have read page that you have suggested. How can i know which problem cause crash. because without knowing the the actual cause of crash , how can i put an anti-dot at {$except} thing? Can you suggest any method to do that. I have made some changes to my code and game is not crashing when i'm standing at any place but when i'm going to start walking, game got crash. in this situation i can not set breakpoint at beginning of my script to know at which code or line my game is crashing. otherwise i bypass that situation by some compare or other thing. Now i need some expert's suggestion like you in this situation. And i haven't seen any {$try}/{$except} script till now so i honestly says i have no knowledge of it.If there is some example script is there, i definitely study that. I also have no idea about "isbadreadptr" thing but i have learned that thing in this topics below.
https://forum.cheatengine.org/viewtopic.php?t=511049
&
https://www.cheatengine.org/forum/viewtopic.php?t=560583&start=0&postdays=0&postorder=asc&highlight=&sid=bb6d1fd00d5ab37d3fed0790867c2cb1
And also can you suggest how can i "keep the stack in a proper condition though". because i have followed OldCheatEngineUser's advice and made some changes to script like this and when i am tracing this code at popad all the registers are restored, prior to this my eax, ecx edx and esp registers are got changed after isbadreadptr kernel calling.
| Code: | pushad
//--------------check edx+8 is valid pointer
lea eax,[edx+8]
push 00000004
push eax
call isbadreadptr
cmp eax,0
popad // because of x86 calling conventions |
|
|
| Back to top |
|
 |
Dark Byte
Site Admin
 Reputation: 458 Reputation: 458
Joined: 09 May 2003
Posts: 25287
Location: The netherlands
|
 Posted: Mon Dec 10, 2018 6:35 am Post subject: Posted: Mon Dec 10, 2018 6:35 am Post subject: |
  |
|
| Code: |
aobscanmodule(health,VictorVranSteam.exe,89 02 8B 41 04 8B 4D F8) // should be unique
alloc(newmem,$1000)
label(code)
label(return)
label(park)
newmem:
push eax //store eax as the code below is going to change it
{$try}
//----------------------check health string
lea eax,[edx+8]
cmp dword ptr[eax+10],'heal' //this can cause an exception
jne park
cmp dword ptr[eax+14],'th' //this can cause an exception
jne park
//-----------if health string then write health
//the code managed to get here, so no exception happened (and the text is 'health' )
jmp itishealthandnocrash
{$except}
//if this gets reached an exception happened which would have crashes the game otherwise, just deal it as no health
jmp park
itishealthandnocrash:
pop eax //undo the push, or use add esp,4
mov eax,3e8
jmp code
park:
pop eax //restore eax
code:
mov [edx],eax
mov eax,[ecx+04]
jmp return
health:
jmp newmem
return:
registersymbol(health)
|
_________________
Do not ask me about online cheats. I don't know any and wont help finding them.
Like my help? Join me on Patreon so i can keep helping |
|
| Back to top |
|
 |
dharmang1910
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 09 May 2010
Posts: 102
|
 Posted: Mon Dec 10, 2018 11:54 am Post subject: Posted: Mon Dec 10, 2018 11:54 am Post subject: |
 |
|
| Dark Byte wrote: | | Code: |
aobscanmodule(health,VictorVranSteam.exe,89 02 8B 41 04 8B 4D F8) // should be unique
alloc(newmem,$1000)
label(code)
label(return)
label(park)
newmem:
push eax //store eax as the code below is going to change it
{$try}
//----------------------check health string
lea eax,[edx+8]
cmp dword ptr[eax+10],'heal' //this can cause an exception
jne park
cmp dword ptr[eax+14],'th' //this can cause an exception
jne park
//-----------if health string then write health
//the code managed to get here, so no exception happened (and the text is 'health' )
jmp itishealthandnocrash
{$except}
//if this gets reached an exception happened which would have crashes the game otherwise, just deal it as no health
jmp park
itishealthandnocrash:
pop eax //undo the push, or use add esp,4
mov eax,3e8
jmp code
park:
pop eax //restore eax
code:
mov [edx],eax
mov eax,[ecx+04]
jmp return
health:
jmp newmem
return:
registersymbol(health)
|
|
Thank you very much for your help, I'll definitely try this and reply what happened to here.
|
|
| Back to top |
|
 |
dharmang1910
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 09 May 2010
Posts: 102
|
 Posted: Thu Dec 13, 2018 12:38 am Post subject: success of script Posted: Thu Dec 13, 2018 12:38 am Post subject: success of script |
 |
|
here is the script i made for this game, all credits goes to Dark byte for his great help regarding {$try}/{$except} thing and i also give him a big thanks from teaching me a great thing.
| Code: | [ENABLE]
aobscanmodule(INJECT,VictorVranSteam.exe,00 8B 01 89 06 8B 41 04) // should be unique
alloc(newmem,$1000)
label(code)
label(return)
label(park)
label(nocrash)
newmem:
push eax
{$try}
mov eax,[ecx+8]
test eax,eax
je park
cmp [eax+10],74696E49
jne park
cmp [eax+14],486C6169
jne park
jmp nocrash
{$except}
jmp park
nocrash:
pop eax
mov [ecx],#1000000
jmp code
park:
pop eax //restore eax
code:
mov eax,[ecx]
mov [esi],eax
mov eax,[ecx+04]
jmp return
INJECT+01:
jmp newmem
nop
nop
return:
registersymbol(INJECT)
|
|
|
| Back to top |
|
 |
|
|
You cannot post new topics in this forum
You cannot reply to topics in this forum
You cannot edit your posts in this forum
You cannot delete your posts in this forum
You cannot vote in polls in this forum
You cannot attach files in this forum
You can download files in this forum
|
|

 Reputation: 198
Reputation: 198 Reputation: 20
Reputation: 20 Reputation: 20
Reputation: 20 Reputation: 20
Reputation: 20 Reputation: 458
Reputation: 458 Reputation: 458
Reputation: 458