|
Cheat Engine
The Official Site of Cheat Engine
|
| View previous topic :: View next topic |
| Author |
Message |
skynet888
!BEWARE! Deletes post on answer
![]() Reputation: 1 Reputation: 1
Joined: 12 Apr 2021
Posts: 57
|
 Posted: Thu May 19, 2022 7:03 pm Post subject: Why doesn't [Break and Trace] show the previous Instruction? Posted: Thu May 19, 2022 7:03 pm Post subject: Why doesn't [Break and Trace] show the previous Instruction? |
 |
|
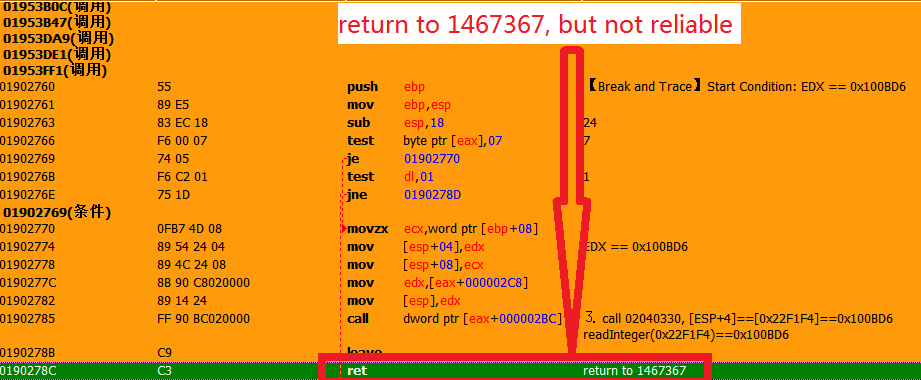
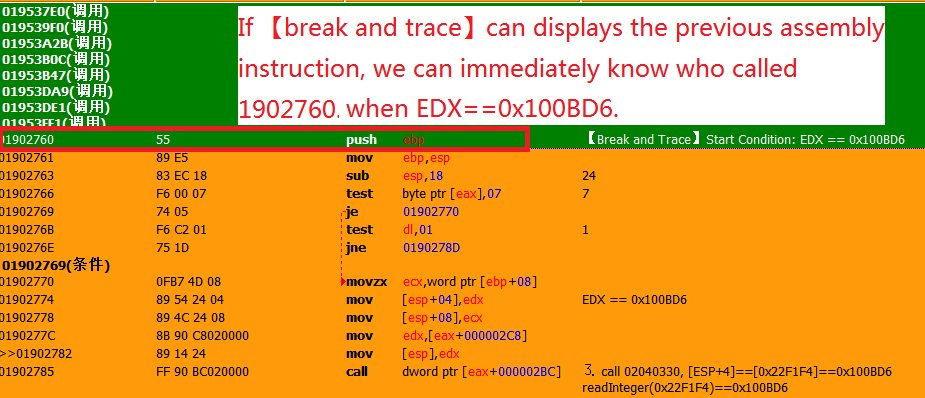
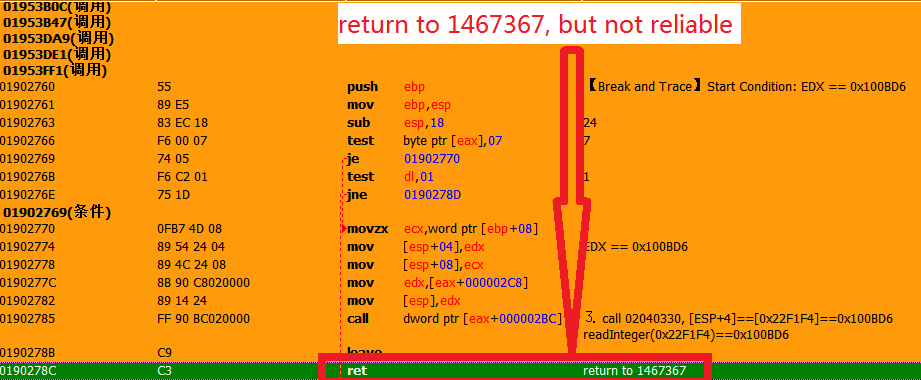
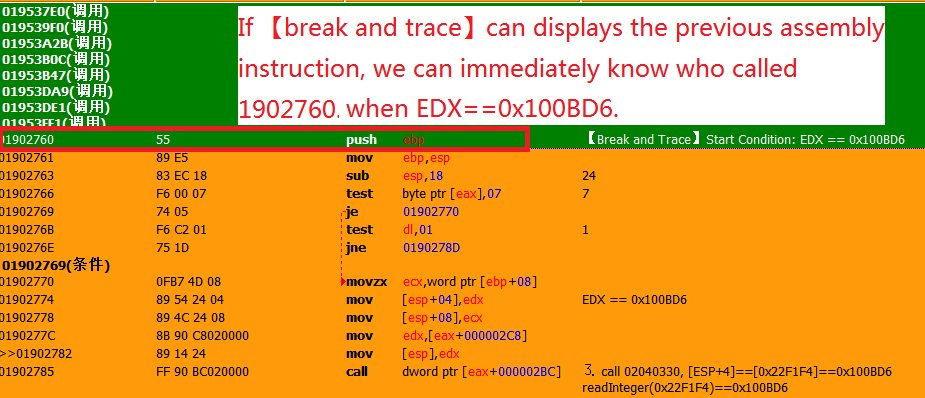
Why doesn't it show the previous assembly instruction? As the picture below shows: if [break and trace] support displaying the previous instruction before 1902760, we can quickly and easily know who called 1902760 when EDX==0x100BD6.But currently it only displays instructions after 1902760.
You will probably suggest to me: "You can trace it until the function returns and you will know who called 1902760". But you are wrong, the function returns to 1467367, but if you set the conditional breakpoint "EDX==0x100BD6" at 1467364, you will not get any result. Why? Because 1467364 may first call address A, address A modified EDX to 0x100BD6, and then jmp to 1902760. So the method of tracking to the function return is not reliable. The fastest and most reliable way is to let CE itself show who called 1902760 when EDX==0x100BD6
PS:Please look at the picture in numerical order: first look at 111111.png then look at 2222222.png, and finally look at 3333333.png
| Description: |
|
| Filesize: |
38.04 KB |
| Viewed: |
744 Time(s) |

|
| Description: |
|
| Filesize: |
34.05 KB |
| Viewed: |
744 Time(s) |
|
| Description: |
|
| Filesize: |
38.37 KB |
| Viewed: |
764 Time(s) |
|
|
|
| Back to top |
|
 |
TsTg
Master Cheater
 Reputation: 5 Reputation: 5
Joined: 12 Dec 2012
Posts: 334
Location: Somewhere....
|
 Posted: Thu May 19, 2022 11:39 pm Post subject: Posted: Thu May 19, 2022 11:39 pm Post subject: |
 |
|
in picture 1 i see edx is getting overwritten from [eax+2C8], then pushed to the stack, then followed by the call to [eax+2BC], you can put a breakpoint there at 1902785 (DONT enter to the call), but setting the condition [esp] == 0x100BD6 instead, however i dont really recommend doing that since this is a dynamic code and [eax+2BC] could lead to some other function.
you can run and stop at 2040330, put a breakpoint with the condition [ESP+4] == 0x100BD6 right there too.
|
|
| Back to top |
|
 |
skynet888
!BEWARE! Deletes post on answer
![]() Reputation: 1 Reputation: 1
Joined: 12 Apr 2021
Posts: 57
|
 Posted: Fri May 20, 2022 12:12 am Post subject: Posted: Fri May 20, 2022 12:12 am Post subject: |
 |
|
| TsTg wrote: | in picture 1 i see edx is getting overwritten from [eax+2C8], then pushed to the stack, then followed by the call to [eax+2BC], you can put a breakpoint there at 1902785 (DONT enter to the call), but setting the condition [esp] == 0x100BD6 instead, however i dont really recommend doing that since this is a dynamic code and [eax+2BC] could lead to some other function.
you can run and stop at 2040330, put a breakpoint with the condition [ESP+4] == 0x100BD6 right there too. |
Thank you my friend, I may not have expressed myself clearly. Now, it is known that the value of [ESP+4] is assigned by EDX. So, my goal is to continue to look upward to find who assigned the value to EDX. That is, my goal is to look upward - to find the instruction that jumps to 1902760 (EDX==0x100BD6 when jumping to 1902760).
|
|
| Back to top |
|
 |
TsTg
Master Cheater
 Reputation: 5 Reputation: 5
Joined: 12 Dec 2012
Posts: 334
Location: Somewhere....
|
 Posted: Fri May 20, 2022 2:22 am Post subject: Posted: Fri May 20, 2022 2:22 am Post subject: |
 |
|
then and from picture 3, you can see EDX is being edited at the start there (at146732D) , if not, it could be assigned after the call to [ebx+230] (at 146734C), take a look at the very top code, or the start of the function itself, perhaps the actual target value you need to look for is not 0x100BD6.
is this a Unreal Engine or a Unity game by any chance ?, this kind of dynamic code is used alot by those engines.
|
|
| Back to top |
|
 |
|
|
You cannot post new topics in this forum
You cannot reply to topics in this forum
You cannot edit your posts in this forum
You cannot delete your posts in this forum
You cannot vote in polls in this forum
You cannot attach files in this forum
You can download files in this forum
|
|

 Reputation: 5
Reputation: 5 Reputation: 5
Reputation: 5