| View previous topic :: View next topic |
| Author |
Message |
LongBeardedLion
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 10 Apr 2020
Posts: 172
|
 Posted: Tue May 26, 2020 10:48 am Post subject: Trying to call a function to attack in a specific way Posted: Tue May 26, 2020 10:48 am Post subject: Trying to call a function to attack in a specific way |
 |
|
Hi. Im modding a rts to make units attack in a different way depending on the situation.
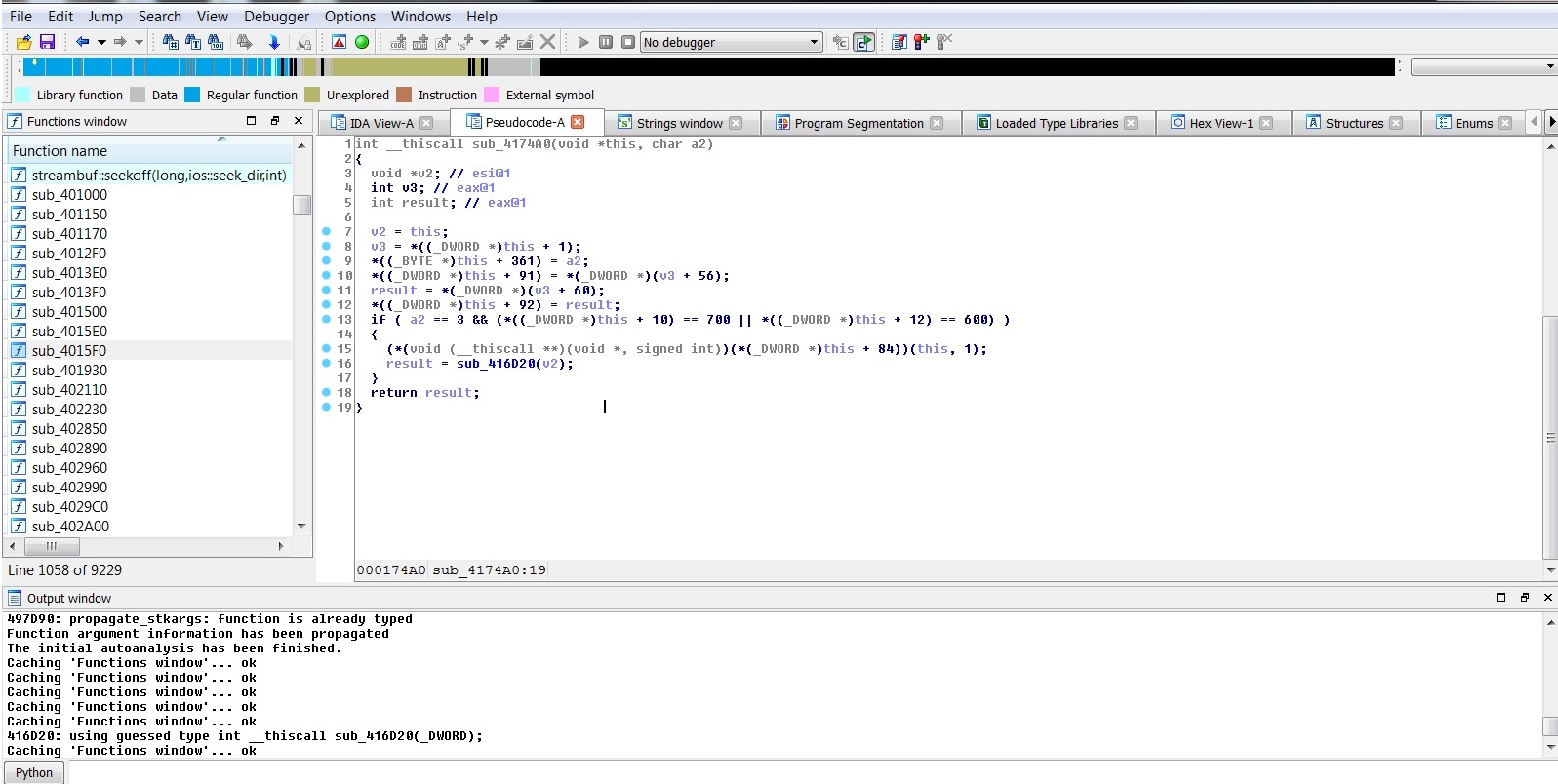
I found the function and then the address in the stack with the value with OllyDbg and Ida Pro.
The function address is 4174A0. The attack stance type is in the stack at 12D5D4.
So far this is great. I learned how to call functions with Guided Hacking tutorials. But i still dont know how am i going to change that value in the stack. Or if that is even possible? What should i do?
Changing that value in the stack will change the Attack stance. But also it seems that the value in the stack corresponds to the argument in the function.
Should i call the function and somehow change the argument? Should i call the function and change the function inside to change the argument inside? Or is there a way to change that value in the stack when the function is called?
Pls help. Thank you
| Description: |
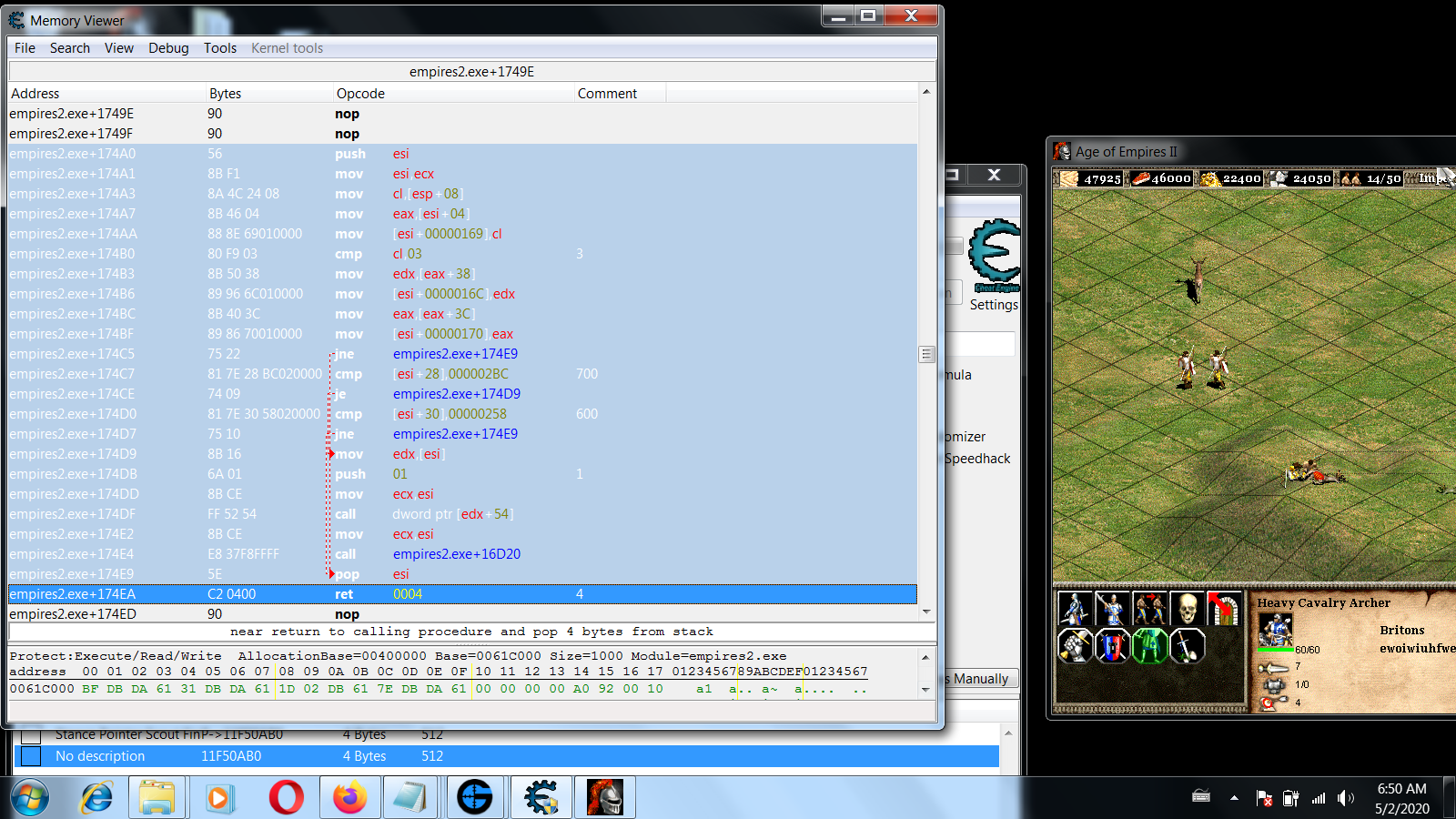
| The function selected in Cheat Engine. |
|
| Filesize: |
510.56 KB |
| Viewed: |
1131 Time(s) |
|
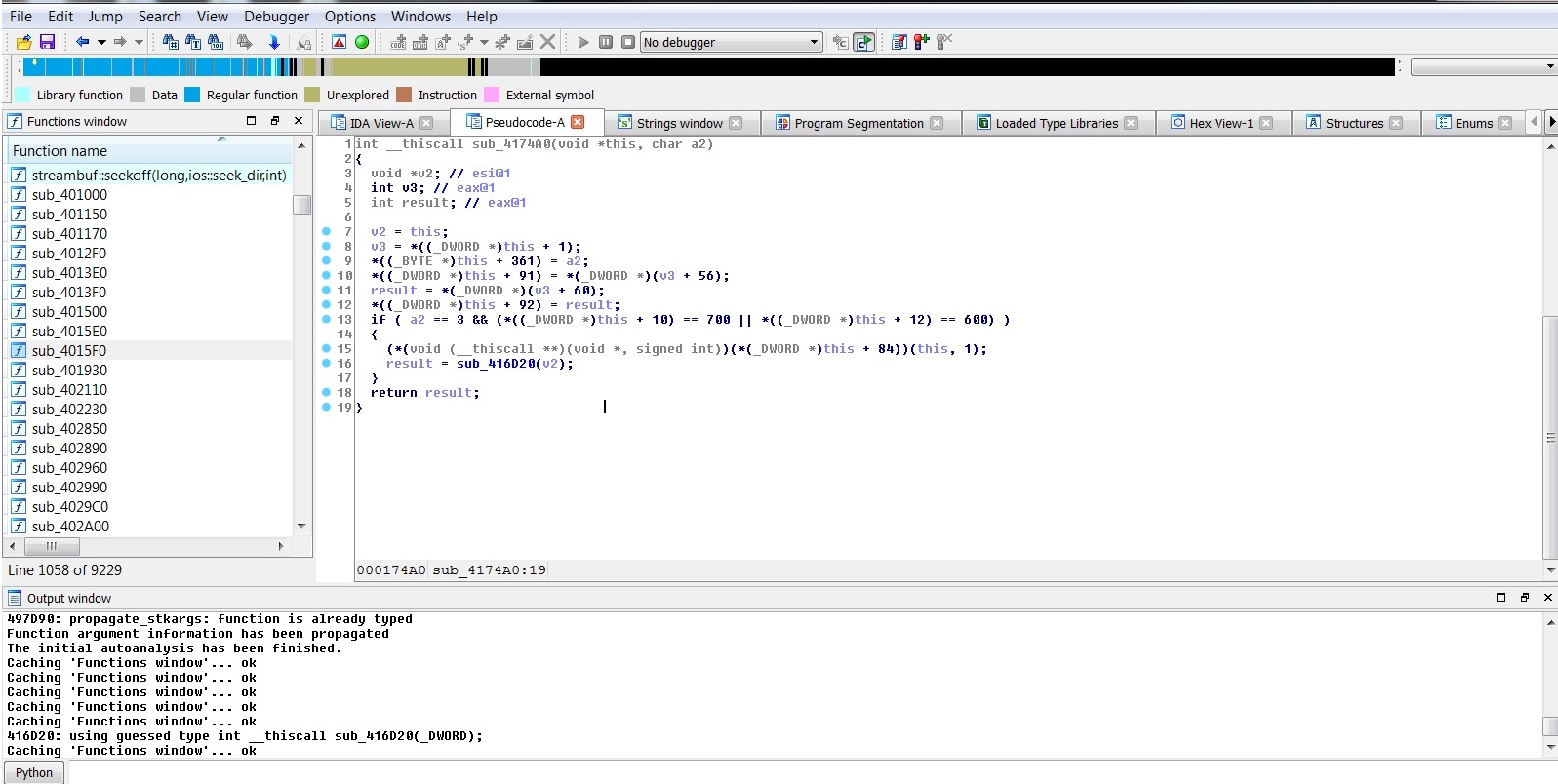
| Description: |
| This is the function that change the stance. a2 corresponds to the argument that will change the attack stance. That seems to have a relation with the value in the stack. |
|
| Filesize: |
265.53 KB |
| Viewed: |
1131 Time(s) |
|
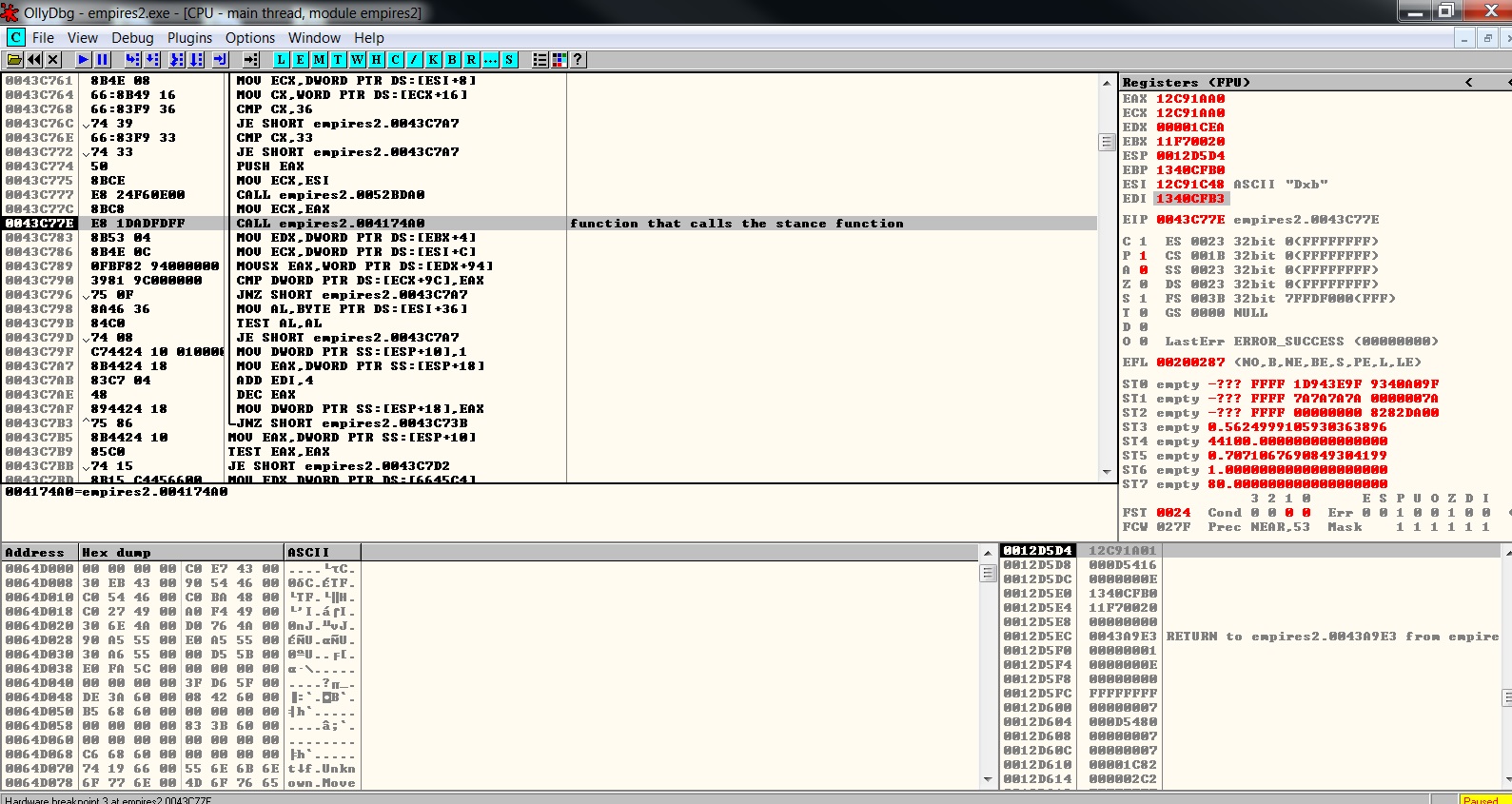
| Description: |
| As you can see here the value pointed at in the stack, will change the Attack stance value. So if i write 12CB0900 it will attack in a certain way and 12CB0901 in another. |
|
| Filesize: |
428.17 KB |
| Viewed: |
1131 Time(s) |

|
|
|
| Back to top |
|
 |
ParkourPenguin
I post too much
 Reputation: 140 Reputation: 140
Joined: 06 Jul 2014
Posts: 4299
|
 Posted: Tue May 26, 2020 11:55 am Post subject: Posted: Tue May 26, 2020 11:55 am Post subject: |
 |
|
You can make a code injection at the start of the function if you want.
e.g. basic example:
| Code: | [ENABLE]
aobscanmodule(ChangeStanceInject,empires2.exe,56 8B F1 8a 4c 24 08) // should be unique
alloc(newmem,1024)
alloc(moveStance,4)
label(return)
registersymbol(ChangeStanceInject)
registersymbol(moveStance)
newmem:
mov esi,ecx
mov cl,[moveStance]
jmp return
ChangeStanceInject+1:
jmp newmem
nop
return:
[DISABLE]
ChangeStanceInject+1:
db 8B F1 8A 4C 24 08
unregistersymbol(moveStance)
unregistersymbol(ChangeStanceInject)
dealloc(moveStance)
dealloc(newmem)
|
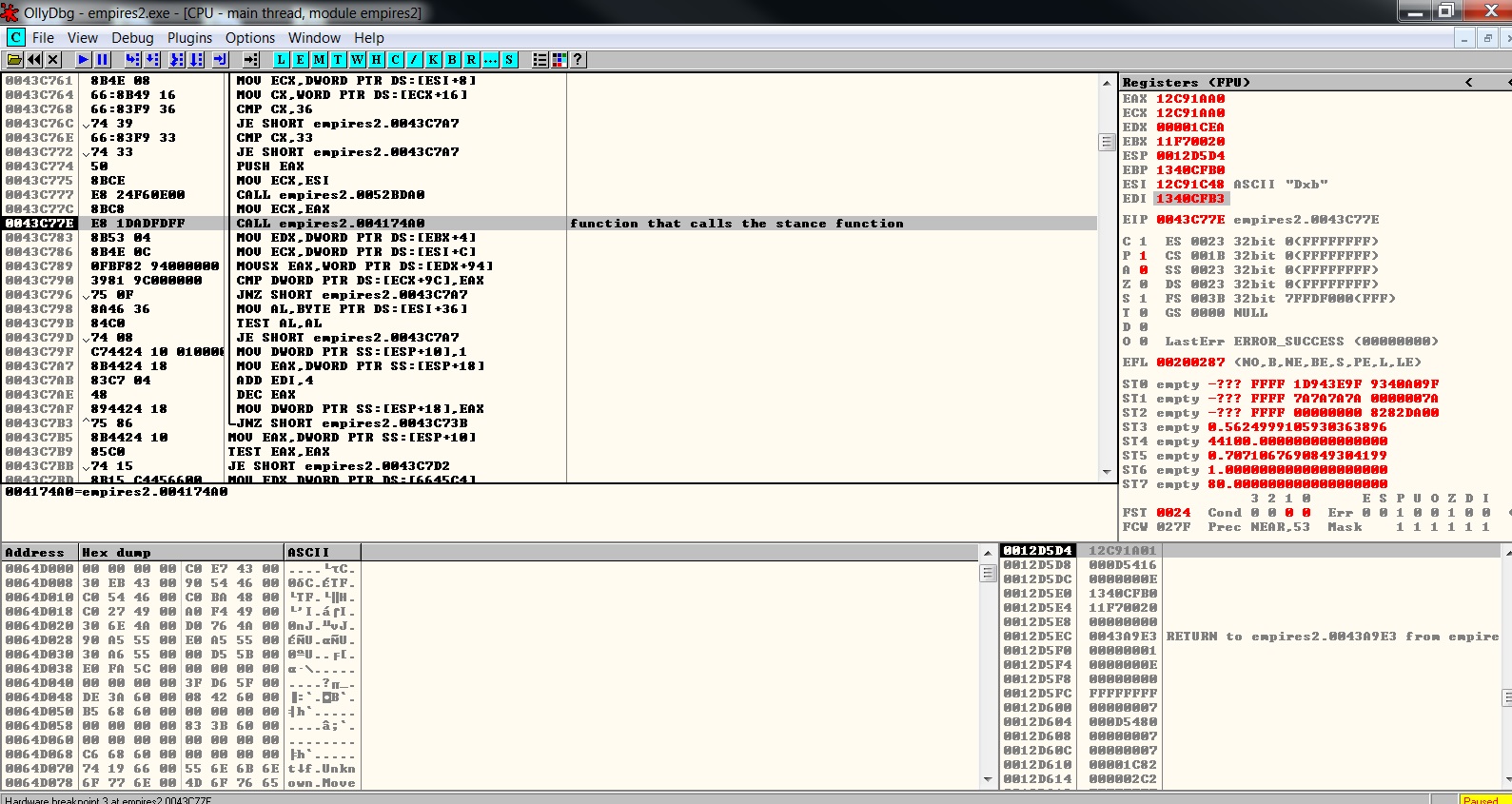
Alternatively, find calls to the function and change the argument(s) there. In CE you'd use Tools -> Dissect Code on the exe, then look at Empires2.exe+174A0 and see what calls it.
You could also set a breakpoint and look at the return address the call left on the stack.
_________________
I don't know where I'm going, but I'll figure it out when I get there. |
|
| Back to top |
|
 |
LongBeardedLion
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 10 Apr 2020
Posts: 172
|
 Posted: Wed May 27, 2020 3:27 am Post subject: Posted: Wed May 27, 2020 3:27 am Post subject: |
 |
|
Thank you ParkourPenguin.
So you are basically overwritting CL? Or you are just adding in code to the function?
Your example seems simple and effective i will test with it first. But i have little experience with injection in cheat engine.
I want it to make a c++ injection, which i more familiarized with. But thats too much for now.
>Alternatively, find calls to the function and change the argument(s) there. In CE you'd use Tools -> Dissect Code on the exe, then look at Empires2.exe+174A0 and see what calls it.
You could also set a breakpoint and look at the return address the call left on the stack.
I have that already. I have all the functions that lead to this function. But i dont understand how can i get the arguments out of it:
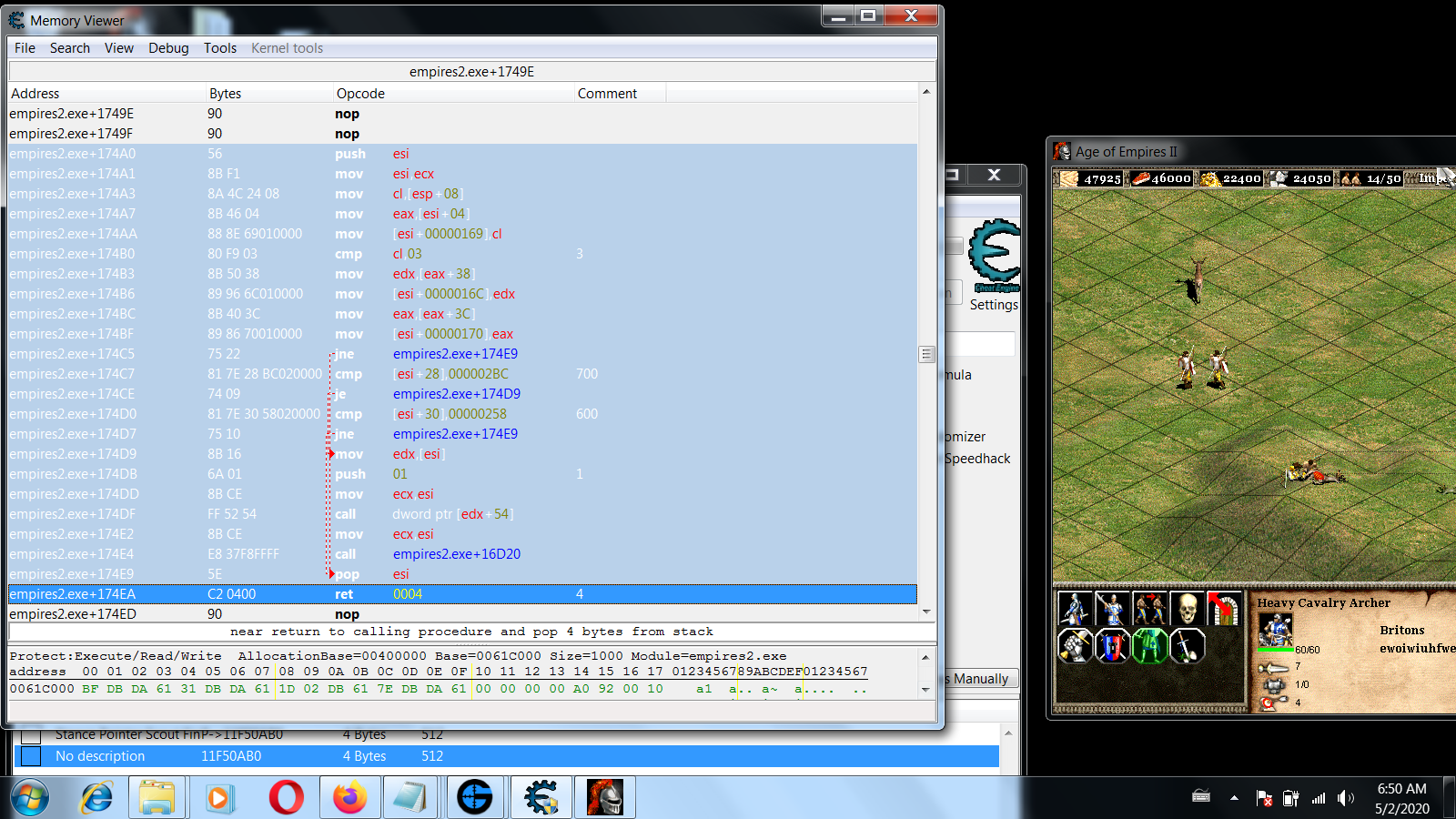
That address in the image below is what calls our function 4174A0.
How do i check the argument that is being passed? I feel like a monkey looking at it.
| Description: |
|
| Filesize: |
429.6 KB |
| Viewed: |
1091 Time(s) |
|
|
|
| Back to top |
|
 |
ParkourPenguin
I post too much
 Reputation: 140 Reputation: 140
Joined: 06 Jul 2014
Posts: 4299
|
 Posted: Wed May 27, 2020 10:49 am Post subject: Posted: Wed May 27, 2020 10:49 am Post subject: |
 |
|
| LongBeardedLion wrote: | | So you are basically overwritting CL? Or you are just adding in code to the function? |
- Find the injection point (aobscan)
- Allocate some memory in the target process (alloc)
- Write come code in that allocated memory (newmem: ...)
- Modify code at the injection point to either jump or call the new code (ChangeStanceInject+1: ...)
| LongBeardedLion wrote: | | But i dont understand how can i get the arguments out of it: |
In the callee, the argument is stored at [esp+8].
[esp] is a backup of esi, [esp+4] is the return address of the call instruction that called this function, and [esi+8] must be a parameter assigned by the caller prior to the call.
If I had to guess, I'd say the push eax instruction does that, but I'm not sure. That might be for the previous call a couple instructions above the call you're interested in.
You should look at that caller function in more detail- particularly inside that loop the call is in. It looks like it could be looping over a collection of units (perhaps selected units) and changing their stance, but that image doesn't show enough to give that statement any more significance than a wild guess.
_________________
I don't know where I'm going, but I'll figure it out when I get there. |
|
| Back to top |
|
 |
|

 Reputation: 140
Reputation: 140 Reputation: 140
Reputation: 140