| View previous topic :: View next topic |
| Author |
Message |
lyaniku
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 26 Aug 2017
Posts: 15
|
 Posted: Tue Jun 04, 2019 8:36 am Post subject: Need help with DBVM/What writes to this address Posted: Tue Jun 04, 2019 8:36 am Post subject: Need help with DBVM/What writes to this address |
 |
|
Hello,
I am trying to figure out where code is written/generated from in a game.
The game that's only running in Usermode generates some code at runtime that I am interested in how it's generated. It's likely happening in one of their TLS callbacks, so my current attempt with Cheat Engine was the following:
1) Start the process and look at what VA the code is when it's generated
2) Restart the game and verify that it always is at the same VA
3) Start the process suspended
4) DBVM Look what writes to this address/VA from above
5) Resume process
Even though I see in the Memory viewer how the bytes at the address change (how the data turns into the code) - there is nothing logged in the DBVM window.
On the other hand, if I look what Reads or Writes to this address, I am getting some results with the same Method. All the read accesses happen before the code is generated though.
So it seems like there is no direct write to that location, my questions are now the following:
1) What other ways has a Ring3 game to put code onto that location, that does not get caught by DBVM?
2) What ways do I have accordingly to still catch it?
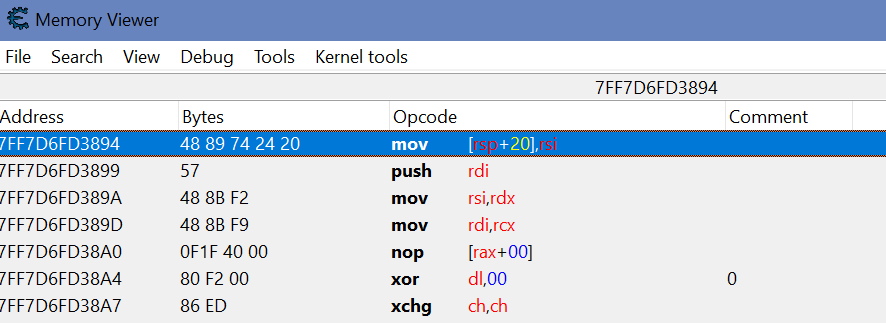
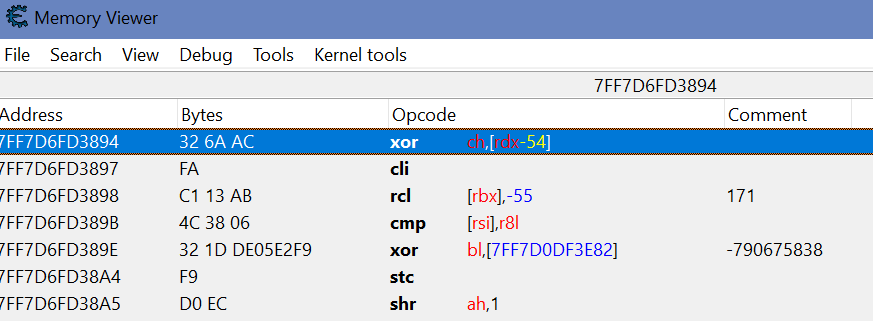
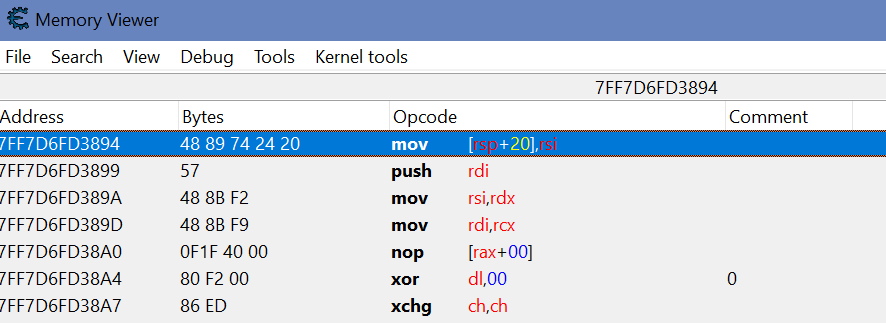
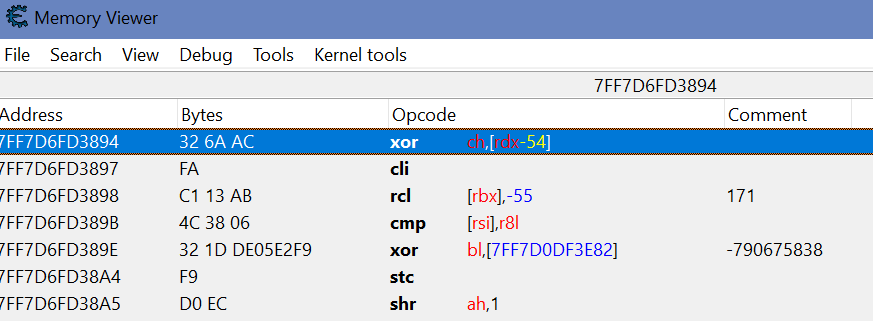
I also attached 2 screenshots, 1 from suspended state, and 1 when the process is loaded.
Oh and the code does definitely not exist in that form directly, a pattern scan doesn't find it and the code is different for every pc too.
Thanks everyone!
| Description: |
|
| Filesize: |
17.7 KB |
| Viewed: |
2886 Time(s) |
|
| Description: |
| in CREATE_SUSPENDED state. |
|
| Filesize: |
17.78 KB |
| Viewed: |
2886 Time(s) |
|
|
|
| Back to top |
|
 |
Dark Byte
Site Admin
 Reputation: 458 Reputation: 458
Joined: 09 May 2003
Posts: 25288
Location: The netherlands
|
 Posted: Tue Jun 04, 2019 8:48 am Post subject: Posted: Tue Jun 04, 2019 8:48 am Post subject: |
 |
|
Does the PA of the VA change between starting it suspended and after resuming?
Because DBVM watches the PA for writes
e.g it could be triggering a COW or even remapping a region
And try the kernelmode debugger interface and then find what writes (not the DBVM one, though you need DBVM to prevent windows from BSODing)
(Won't catch remaps but will catch COW writes)
_________________
Do not ask me about online cheats. I don't know any and wont help finding them.
Like my help? Join me on Patreon so i can keep helping |
|
| Back to top |
|
 |
lyaniku
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 26 Aug 2017
Posts: 15
|
 Posted: Tue Jun 04, 2019 9:07 am Post subject: Posted: Tue Jun 04, 2019 9:07 am Post subject: |
 |
|
I tried using the kernelmode debugger and look what writes to this address, no result again.
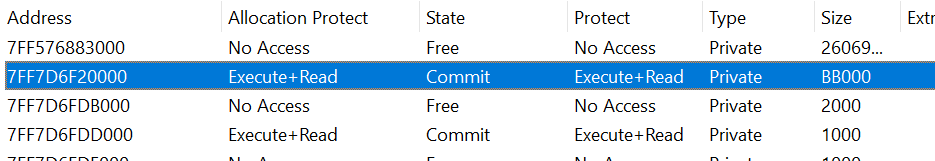
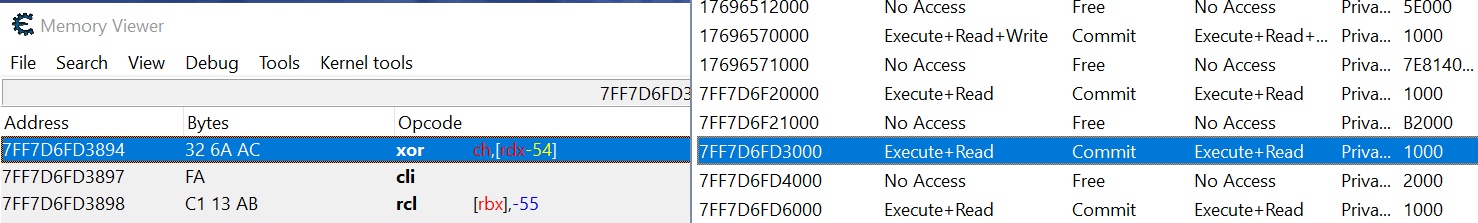
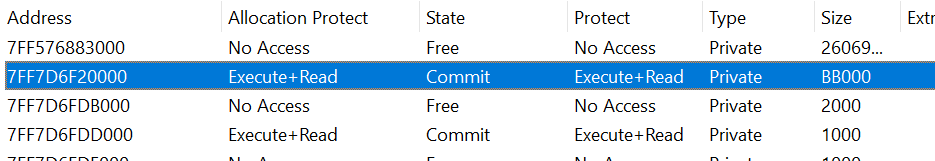
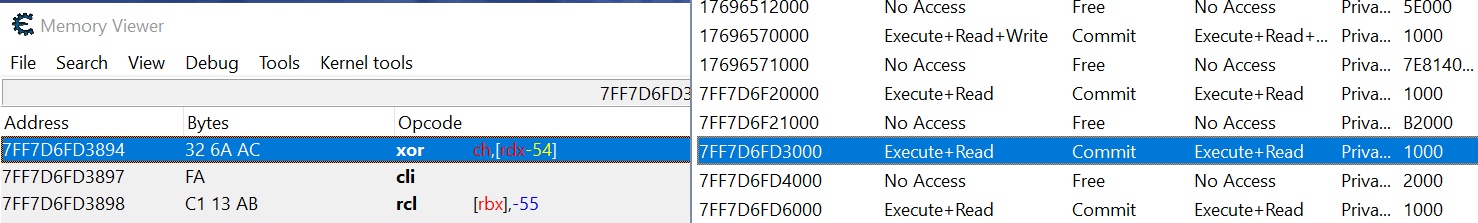
The page does change, I attached 2 screenshots again of before and after loaded.
What do you mean with it could trigger a COW? I don't know what COW means, I'm at beginner level when it comes to kernel mode, Paging.
I know that they are remapping their module with PAGE_EXECUTE_READ and SEC_NOCHANGE.
I don't know enough however, to know how that stops CE from detecting the write. Would CE detect it if they were using NtWriteVirtualMemory for example?
| Description: |
|
| Filesize: |
10.52 KB |
| Viewed: |
2875 Time(s) |
|
| Description: |
|
| Filesize: |
28.07 KB |
| Viewed: |
2875 Time(s) |
|
|
|
| Back to top |
|
 |
Dark Byte
Site Admin
 Reputation: 458 Reputation: 458
Joined: 09 May 2003
Posts: 25288
Location: The netherlands
|
 Posted: Tue Jun 04, 2019 9:40 am Post subject: Posted: Tue Jun 04, 2019 9:40 am Post subject: |
 |
|
Look at the PA, not the VA (PA is shown in the hexview header)
COW is copy on write. It causes windows to allocate a new PA for the region, and copy the contents to there
As for CE not detecting it, is because they aren't writing to the memory.
They just swap the pagetable entry with a new address that contains the memory
_________________
Do not ask me about online cheats. I don't know any and wont help finding them.
Like my help? Join me on Patreon so i can keep helping |
|
| Back to top |
|
 |
lyaniku
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 26 Aug 2017
Posts: 15
|
 Posted: Tue Jun 04, 2019 9:49 am Post subject: Posted: Tue Jun 04, 2019 9:49 am Post subject: |
 |
|
The physical address does change, yes (1ca6a3894 -> bdced894).
Okay that makes sense now that DBVM doesn't catch it to me. And if KM CE catches COW but not remapping, then it has to be remapped... I guess?!
I will try to patch an EB FE after the remapping tomorrow then, and attach CE after.
If anyone has different suggestions on what I can try please reply, I also don't know if the game will just let me do what I said above and how much trouble it will be to make it let it do.
|
|
| Back to top |
|
 |
lyaniku
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 26 Aug 2017
Posts: 15
|
 Posted: Tue Jun 11, 2019 11:51 am Post subject: Posted: Tue Jun 11, 2019 11:51 am Post subject: |
 |
|
Btw. it turned out to be very easy with this information Dark Byte.
I just had to hw:bp ntdll.ZwMapViewOfSection and press F9 and watched the PA until change, and then DBVM what writes to this address returned the repe movsb.
Thanks again.
|
|
| Back to top |
|
 |
|

 Reputation: 458
Reputation: 458 Reputation: 458
Reputation: 458