|
Cheat Engine
The Official Site of Cheat Engine
|
| View previous topic :: View next topic |
| Author |
Message |
Special11
Cheater
![]() Reputation: 0 Reputation: 0
Joined: 20 Dec 2009
Posts: 28
|
 Posted: Thu Aug 26, 2010 2:59 pm Post subject: Static address? Posted: Thu Aug 26, 2010 2:59 pm Post subject: Static address? |
 |
|
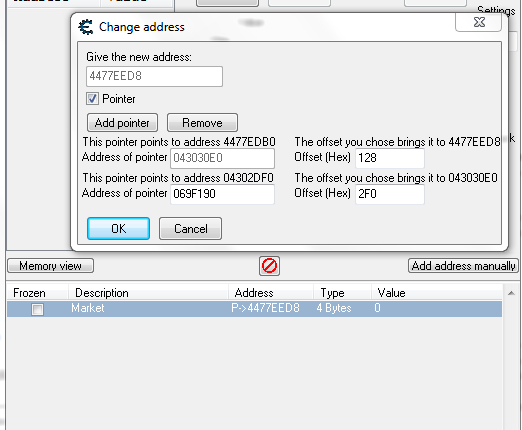
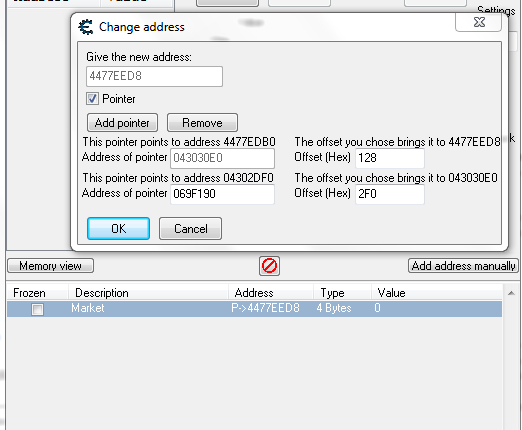
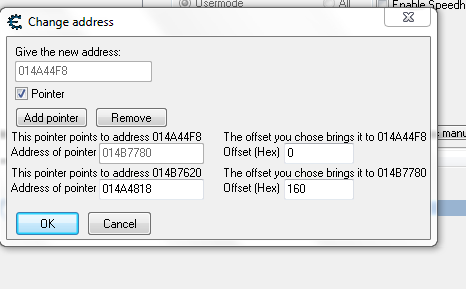
Hello all, well I found pointer that is working every time i run the game, but it isn't address in format like:
[module+offset] ex. [Game.exe+0x4c3]
But like this one in screenshot. ( 069F190 )
Well, i tried to find a real static address like in [module+offset] format but i think that anti-cheat blocks these addresses from scanning.
And my question. Can I use pointer like this one in screenshot to my trainer? Or how can I find the real static address? I tried both method ( pointer scanner and debugger ). And I'm using kernel mode debugger and Read/Write process memory.
| Description: |
|
| Filesize: |
26.85 KB |
| Viewed: |
12181 Time(s) |
|
|
|
| Back to top |
|
 |
Dark Byte
Site Admin
 Reputation: 458 Reputation: 458
Joined: 09 May 2003
Posts: 25295
Location: The netherlands
|
 Posted: Thu Aug 26, 2010 3:48 pm Post subject: Posted: Thu Aug 26, 2010 3:48 pm Post subject: |
  |
|
if it falls in the .exe's region of memory then yes, it'll stay static
_________________
Do not ask me about online cheats. I don't know any and wont help finding them.
Like my help? Join me on Patreon so i can keep helping |
|
| Back to top |
|
 |
Special11
Cheater
![]() Reputation: 0 Reputation: 0
Joined: 20 Dec 2009
Posts: 28
|
 Posted: Thu Aug 26, 2010 4:12 pm Post subject: Posted: Thu Aug 26, 2010 4:12 pm Post subject: |
 |
|
Thank's for help, but why it isn't in static address format? And yes, it is in .exe's memory region, but i can't make it working in C++. (I'm sure that this address work's in CE)
| Code: |
UINT_PTR DeRef( UINT_PTR _uiptrPointer ) {
UINT_PTR uiptrRet;
if ( !::ReadProcessMemory( hProcess, reinterpret_cast<LPVOID>(_uiptrPointer), &uiptrRet, sizeof( uiptrRet ), NULL ) ) { return 0UL; }
return uiptrRet;
}
void multiPointer(unsigned int speed) {
UINT_PTR uiptrFinal = DeRef( DeRef( 0x69F190 ) + 0xA20 ) + 0x9BA;
::WriteProcessMemory( hProcess, reinterpret_cast<LPVOID>(uiptrFinal), &speed, sizeof(speed), NULL );
}
void CMyHackDlg::SpeedButtonOn()
multiPointer(16666);
}
void CMyHackDlg::SpeedButtonOff()
{
multiPointer(16230);
}
|
|
|
| Back to top |
|
 |
justa_dude
Grandmaster Cheater
 Reputation: 23 Reputation: 23
Joined: 29 Jun 2010
Posts: 891
|
 Posted: Thu Aug 26, 2010 5:29 pm Post subject: Posted: Thu Aug 26, 2010 5:29 pm Post subject: |
 |
|
| Is your game crashing when you try to use your snippet? I wonder if you're trying to write to null. It should be pretty easy to debug - just look at the locations your trainer is trying to read / write.
|
|
| Back to top |
|
 |
Special11
Cheater
![]() Reputation: 0 Reputation: 0
Joined: 20 Dec 2009
Posts: 28
|
 Posted: Thu Aug 26, 2010 7:15 pm Post subject: Posted: Thu Aug 26, 2010 7:15 pm Post subject: |
 |
|
Umm well no, when I'm using my trainer just nothing happens. I tested writing memory process by doing this:
| Code: |
UINT_PTR DeRef( UINT_PTR _uiptrPointer ) {
UINT_PTR uiptrRet;
if ( !::ReadProcessMemory( hProcess, reinterpret_cast<LPVOID>(_uiptrPointer), &uiptrRet, sizeof( uiptrRet ), NULL ) ) { return 0UL; }
return uiptrRet;
}
void multiPointer(unsigned int speed) {
UINT_PTR uiptrFinal = DeRef( DeRef( 0x69F190 ) + 0xA20 ) + 0x9BA;
if(!::WriteProcessMemory( hProcess, reinterpret_cast<LPVOID>(uiptrFinal), &speed, sizeof(speed), NULL )) {
MessageBox(NULL,"Error!","4Story",MB_OK);
}
else {
MessageBox(NULL,"Memory written successfully","4Story",MB_OK);
}
}
void CMyHackDlg::SpeedButtonOn()
multiPointer(16666);
}
void CMyHackDlg::SpeedButtonOff()
{
multiPointer(16230);
}
|
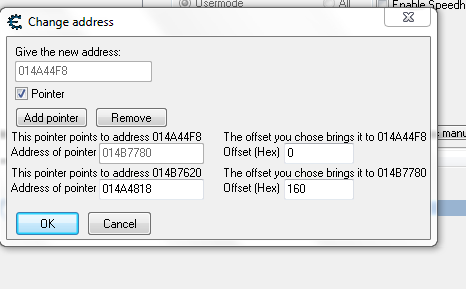
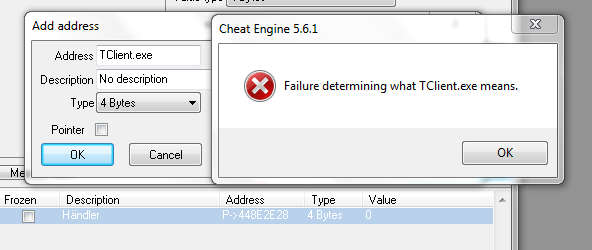
Well but it always show error. Well I tested it on Saper: (pointer on screenshot)
| Code: |
void multiPointer(unsigned int mines) {
UINT_PTR uiptrFinal = DeRef( DeRef( 0x14A4818 ) + 0x160 ) + 0x0;
if(!::WriteProcessMemory( hProcess, reinterpret_cast<LPVOID>(uiptrFinal), &mines, sizeof(mines), NULL )) {
MessageBox(NULL,"Error!","Saper",MB_OK);
}
else {
MessageBox(NULL,"Memory written successfully","Saper",MB_OK);
}
}
|
And it work's! Well i think that when I'm trying to hack 4Story, my trainer is blocked by Hackshield from changing adresses. How can I bypass that? :/
| Description: |
|
| Filesize: |
19.64 KB |
| Viewed: |
12152 Time(s) |
|
|
|
| Back to top |
|
 |
XaLeX
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 19 Aug 2008
Posts: 226
|
 Posted: Thu Aug 26, 2010 8:21 pm Post subject: Posted: Thu Aug 26, 2010 8:21 pm Post subject: |
 |
|
Correct me if i'm wrong, but i thought that any address could be transcribed in the [region+offset] format (e.g. something allocated at address X (say 73cab8) in a region R ("xxx.dll") whose allocbase is Y (700000) would be [R + X-Y] -> [xxx.dll + (73cab8 - 700000)] -> [xxx.dll + 3cab8]).
| Special11 wrote: | | when I'm trying to hack 4Story, my trainer is blocked by Hackshield from changing adresses. How can I bypass that? :/ |
Welcome to hell. No way to hack server sided values with CE; try looking into WPE.
|
|
| Back to top |
|
 |
Special11
Cheater
![]() Reputation: 0 Reputation: 0
Joined: 20 Dec 2009
Posts: 28
|
 Posted: Thu Aug 26, 2010 9:19 pm Post subject: Posted: Thu Aug 26, 2010 9:19 pm Post subject: |
 |
|
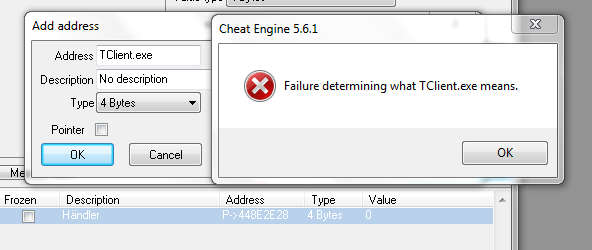
I'm not sure because CE is blocked by Hackshield, even when I'm trying to check .exe base address i can't (look at screenshot) or I'm doing something wrong?
And this address is not server-side value, it work's when changing value in CE, but in my trainer memory writing is blocked by Hackshield.
However, I tried to do basic HS Bypass:
This code should tell HS that everything is right.
| Code: |
UINT MyThreadProc( LPVOID pParam ) {
for (;;){
int EhSvc = (long)GetModuleHandleA("EhSvc.dll");
if(EhSvc !=0){
DWORD OldProtect;
int EhPtr = (0xD1E44);
int Memory1 =(EhSvc+0xD4328);//HS-Addy
int Memory2 =(EhSvc+0xD4334);//Hs-Addy-Jump
int Memory3 =(EhSvc+0xD5A88);//Hs-Addy-Jump
int Memory4 =(EhSvc+0xD5AD4);//Hs-Addy-Jump
int Memory5 =(EhSvc+0xD5B04);//Hs-Addy-Jump
int Memory6 =(EhSvc+0xCA2EC);//Hs-Addy-Jump
int Memory7 =(EhSvc+0xC92F8);//Hs-Addy-Jump
int Memory8 =(EhSvc+0xD0AC8);//Hs-Addy-Jump
int Memory9 = (EhSvc+0xCA2EC);//Hs-Addy-Jump
int Memory10 =(EhSvc+0xD5B04);//Hs-Addy-Jump
int Memory11 =(EhSvc+0xD5B0C);//Hs-Addy-Jump
int Memory12 =(EhSvc+0xC92FC);//Hs-Addy-Jump
int Memory13 =(EhSvc+0xC92F4);//Hs-Addy-Jump
int Memory14 =(EhSvc+0xD4340);//Hs-Addy-Jump
int Memory15 =(EhSvc+0xD0680);//Hs-Addy-Jump
int Memory16 =(EhSvc+0xD3E28);//Hs-Addy-Jump
int Memory17 =(EhSvc+0xD3E48);//Hs-Addy-Jump
int Memory18 =(EhSvc+0xD691C);//Hs-Addy-Jump
int Memory19 =(EhSvc+0xCA2EC);//Hs-Addy-Jump
int Memory20 =(EhSvc+0xD5ACC);//Hs-Addy-Jump
int Memory21 =(EhSvc+0xD43C4);//Hs-Addy-Jump
int Memory22 =(EhSvc+0xD4334);//Hs-Addy-Jump
VirtualProtect((void*)(Memory1),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory1) = 4;
VirtualProtect((void*)(Memory2),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory2) = 4;
VirtualProtect((void*)(Memory3),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory3) = 4;
VirtualProtect((void*)(Memory4),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory4) = 4;
VirtualProtect((void*)(Memory5),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory5) = 4;
VirtualProtect((void*)(Memory6),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory6) = 4;
VirtualProtect((void*)(Memory7),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory7) = 4;
VirtualProtect((void*)(Memory8),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory8) = 4;
VirtualProtect((void*)(Memory9),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory9) = 4;
VirtualProtect((void*)(Memory10),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory10) = 4;
VirtualProtect((void*)(Memory11),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory11) = 4;
VirtualProtect((void*)(Memory12),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory12) = 4;
VirtualProtect((void*)(Memory13),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory13) = 4;
VirtualProtect((void*)(Memory14),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory14) = 4;
VirtualProtect((void*)(Memory15),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory15) = 4;
VirtualProtect((void*)(Memory16),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory16) = 4;
VirtualProtect((void*)(Memory17),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory17) = 4;
VirtualProtect((void*)(Memory18),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory18) = 4;
VirtualProtect((void*)(Memory19),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory19) = 4;
VirtualProtect((void*)(Memory20),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory20) = 4;
VirtualProtect((void*)(Memory21),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory21) = 4;
VirtualProtect((void*)(Memory22),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
*(DWORD*)(Memory22) = 4;
//VirtualProtect((void*)(Memory23),0x6,PAGE_EXECUTE_READWRITE,&OldProtect);
}
Sleep(5);
}
}
|
But it's does not matter, my hack still not work's and Writeprocessmemory fail's, how can I use VirtualProtect method to write something in a memory? Or any other way to unlock Read/Writeprocessmemory?
E: Again I tested this bypass and this code is not applied because my program can't get base address of EhSvc.dll module :/
| Description: |
|
| Filesize: |
27.56 KB |
| Viewed: |
12136 Time(s) |
|
|
|
| Back to top |
|
 |
|
|
You cannot post new topics in this forum
You cannot reply to topics in this forum
You cannot edit your posts in this forum
You cannot delete your posts in this forum
You cannot vote in polls in this forum
You cannot attach files in this forum
You can download files in this forum
|
|

 Reputation: 458
Reputation: 458 Reputation: 23
Reputation: 23