|
Cheat Engine
The Official Site of Cheat Engine
|
| View previous topic :: View next topic |
| Author |
Message |
Twistedfate
Expert Cheater
 Reputation: 1 Reputation: 1
Joined: 11 Mar 2016
Posts: 231
|
 Posted: Sat Apr 22, 2017 6:56 am Post subject: how to get base address of pointer from AOB signature ? Posted: Sat Apr 22, 2017 6:56 am Post subject: how to get base address of pointer from AOB signature ? |
 |
|
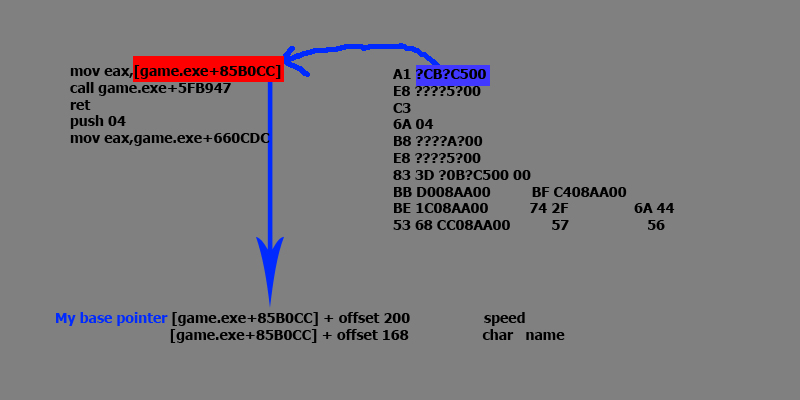
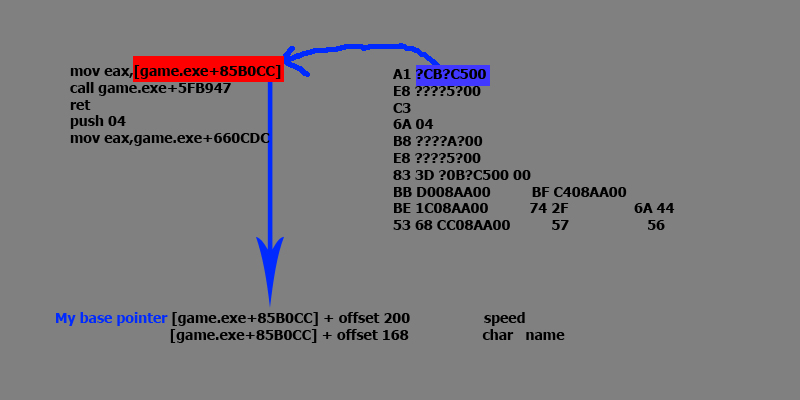
The Idea in the picture .
My base address pointer is [game.exe+85B0CC] its stored inside this signature :
A1 4CB4C500 .
The question is >
is that possible to get the pointer base address from the signature in the picture ... How can I calculate module offset ?
| Code: | | [game.exe+85B0CC] → 4CB4C500 how to get 85B0CC from 4CB4C500 . |
-and how to but it into my pointer ? if that is possible .
- the pointer changes every time so I need to read original bytes after scanning on
| Description: |
|
| Filesize: |
66.3 KB |
| Viewed: |
12484 Time(s) |
|
|
|
| Back to top |
|
 |
mgr.inz.Player
I post too much
 Reputation: 218 Reputation: 218
Joined: 07 Nov 2008
Posts: 4438
Location: W kraju nad Wisla. UTC+01:00
|
 Posted: Sat Apr 22, 2017 8:31 am Post subject: Posted: Sat Apr 22, 2017 8:31 am Post subject: |
  |
|
If it is 32bit process this should do the trick, AA script:
| Code: | [ENABLE]
aobscan(theAob,A1 ?C B? C5 00 E8 ?? ?? 5? 00 C3 6A 04)
label(pointerBase)
registersymbol(pointerBase)
[theAob+1]:
pointerBase:
[DISABLE]
unregistersymbol(pointerBase) |
And use pointerBase symbol as base.
_________________
|
|
| Back to top |
|
 |
ParkourPenguin
I post too much
 Reputation: 140 Reputation: 140
Joined: 06 Jul 2014
Posts: 4299
|
|
| Back to top |
|
 |
Twistedfate
Expert Cheater
 Reputation: 1 Reputation: 1
Joined: 11 Mar 2016
Posts: 231
|
 Posted: Sat Apr 22, 2017 9:55 am Post subject: Posted: Sat Apr 22, 2017 9:55 am Post subject: |
 |
|
mgr.inz.Player
Thnx in advance . but its 64 bit >> I get error not all code injectable
and do u have any script contain full example of your trick ?
|
|
| Back to top |
|
 |
panraven
Grandmaster Cheater
![]() Reputation: 55 Reputation: 55
Joined: 01 Oct 2008
Posts: 942
|
 Posted: Sat Apr 22, 2017 10:09 am Post subject: Posted: Sat Apr 22, 2017 10:09 am Post subject: |
 |
|
Given mgr.inz.Player's code , OP want the offset value as pointerBase - module_base .
ie.
| Code: |
[theAob+1]-moduleAddr: // *
offsetValue:
|
however the * will not evaluated if moduleAddr is a Label or Symbolic address , but it does work if moduleAddr is a hexadecimal number.
The module address can be evaluated/known before hand by Lua eg.
| Code: |
{$lua}
local xbase = readInteger(process)and GetAddress(process)
return xbase and string.format("define(moduleAddr,%X)",xbase)
{$asm}
[ENABLE]
aobscanmodule(theAob,$process,a1 ?? ?? ?? ?? 8b ?? ?? 57)
// another aob pattern for my own test, but not matter here
label(pointerBase)
registersymbol(pointerBase)
label(offsetValue)
registersymbol(offsetValue)
[theAob+1]:
pointerBase: // eg. 41a3a4 in my test
[theAob+1]-moduleAddr:
offsetValue: // give 1a3a4 in my test
[DISABLE]
unregistersymbol(pointerBase)
unregistersymbol(offsetValue)
|
for 64 bit case, it may need to read the RIP address offset as 4 bytes (signed/unsigned?) integer, pure AA symbolic address operation may not be enough at the moment.
Here a custom lookup function is made to read some Lua expression as symbolic address :
| Code: |
{$lua}
if _myLookup then
unregisterSymbolLookupCallback(_myLookup)
end
_myLookup = registerSymbolLookupCallback(function(s)
local LUA_expr = s:match"^%s*%(%?%s*([^?]-)%s*%?%)%s*$"
if LUA_expr then
local ok,try = pcall(load,'return '..LUA_expr,'_',nil,_G)
if ok then ok, try = pcall(try) end
if ok then
local t = type(try)
if t=='number' then
return try
elseif t == 'string' then
return readInteger(try)and GetAddress(try)
end
end
end
end, slFailure)
{$asm}
{$lua}
local xbase = readInteger(process)and GetAddress(process)
return xbase and string.format("define(moduleAddr,%X)",xbase)
{$asm}
[ENABLE]
aobscanmodule(theAob,$process,48 8d 15 ?? ?? ?? ?? e8)
// at cheatengine-x86_64.exe+3b6d
label(pointerBase)
registersymbol(pointerBase)
label(offsetValue)
registersymbol(offsetValue)
(?readInteger(GetAddress'theAob'+3)+GetAddress'theAob'+7?):
pointerBase:
(?readInteger(GetAddress'theAob'+3)+GetAddress'theAob'+7-tonumber('moduleAddr',16)?):
offsetValue:
[DISABLE]
unregistersymbol(pointerBase)
unregistersymbol(offsetValue)
|
The lua expression is awfully look, but if understand the concept, it is fairly easy to express the want address .
_________________
- Retarded. |
|
| Back to top |
|
 |
Twistedfate
Expert Cheater
 Reputation: 1 Reputation: 1
Joined: 11 Mar 2016
Posts: 231
|
 Posted: Sat Apr 22, 2017 12:56 pm Post subject: Posted: Sat Apr 22, 2017 12:56 pm Post subject: |
 |
|
mgr.inz.Player ParkourPenguin mr panraven
thank you all I got it ^^
|
|
| Back to top |
|
 |
xxhehe
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 11 Mar 2015
Posts: 136
|
 Posted: Wed Oct 03, 2018 6:39 am Post subject: Posted: Wed Oct 03, 2018 6:39 am Post subject: |
 |
|
| panraven wrote: | Given mgr.inz.Player's code , OP want the offset value as pointerBase - module_base .
ie.
| Code: |
[theAob+1]-moduleAddr: // *
offsetValue:
|
however the * will not evaluated if moduleAddr is a Label or Symbolic address , but it does work if moduleAddr is a hexadecimal number.
The module address can be evaluated/known before hand by Lua eg.
| Code: |
{$lua}
local xbase = readInteger(process)and GetAddress(process)
return xbase and string.format("define(moduleAddr,%X)",xbase)
{$asm}
[ENABLE]
aobscanmodule(theAob,$process,a1 ?? ?? ?? ?? 8b ?? ?? 57)
// another aob pattern for my own test, but not matter here
label(pointerBase)
registersymbol(pointerBase)
label(offsetValue)
registersymbol(offsetValue)
[theAob+1]:
pointerBase: // eg. 41a3a4 in my test
[theAob+1]-moduleAddr:
offsetValue: // give 1a3a4 in my test
[DISABLE]
unregistersymbol(pointerBase)
unregistersymbol(offsetValue)
|
for 64 bit case, it may need to read the RIP address offset as 4 bytes (signed/unsigned?) integer, pure AA symbolic address operation may not be enough at the moment.
Here a custom lookup function is made to read some Lua expression as symbolic address :
| Code: |
{$lua}
if _myLookup then
unregisterSymbolLookupCallback(_myLookup)
end
_myLookup = registerSymbolLookupCallback(function(s)
local LUA_expr = s:match"^%s*%(%?%s*([^?]-)%s*%?%)%s*$"
if LUA_expr then
local ok,try = pcall(load,'return '..LUA_expr,'_',nil,_G)
if ok then ok, try = pcall(try) end
if ok then
local t = type(try)
if t=='number' then
return try
elseif t == 'string' then
return readInteger(try)and GetAddress(try)
end
end
end
end, slFailure)
{$asm}
{$lua}
local xbase = readInteger(process)and GetAddress(process)
return xbase and string.format("define(moduleAddr,%X)",xbase)
{$asm}
[ENABLE]
aobscanmodule(theAob,$process,48 8d 15 ?? ?? ?? ?? e8)
// at cheatengine-x86_64.exe+3b6d
label(pointerBase)
registersymbol(pointerBase)
label(offsetValue)
registersymbol(offsetValue)
(?readInteger(GetAddress'theAob'+3)+GetAddress'theAob'+7?):
pointerBase:
(?readInteger(GetAddress'theAob'+3)+GetAddress'theAob'+7-tonumber('moduleAddr',16)?):
offsetValue:
[DISABLE]
unregistersymbol(pointerBase)
unregistersymbol(offsetValue)
|
The lua expression is awfully look, but if understand the concept, it is fairly easy to express the want address . |
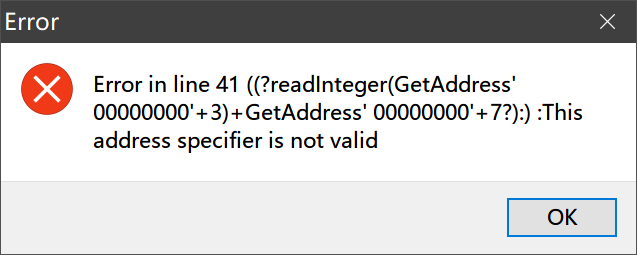
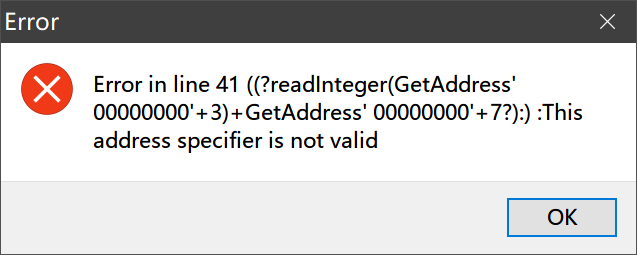
CE6.8.1 X64
x64 process
file-->Assign to current cheat table
| Description: |
|
| Filesize: |
14.59 KB |
| Viewed: |
5703 Time(s) |
|
|
|
| Back to top |
|
 |
|
|
You cannot post new topics in this forum
You cannot reply to topics in this forum
You cannot edit your posts in this forum
You cannot delete your posts in this forum
You cannot vote in polls in this forum
You cannot attach files in this forum
You can download files in this forum
|
|

 Reputation: 1
Reputation: 1 Reputation: 218
Reputation: 218 Reputation: 140
Reputation: 140 Reputation: 1
Reputation: 1 Reputation: 1
Reputation: 1