| View previous topic :: View next topic |
| Author |
Message |
Viloresi
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 02 Feb 2017
Posts: 149
|
 Posted: Thu Apr 06, 2017 2:50 pm Post subject: What can I do if VirtualProtect fails? Posted: Thu Apr 06, 2017 2:50 pm Post subject: What can I do if VirtualProtect fails? |
 |
|
Hello, I'm trying to write into an address, in the memory of a game, that has read-only protection ( it's an opcode).
So I'm trying to use VirtualProtect to change the protection to EXECUTE_READWRITE ...
I'm kinda sure that this game as some kind of protection that is causing the virtualprotect to fail.
Does somebody has an Idea or a bypass for this??
|
|
| Back to top |
|
 |
atom0s
Moderator
 Reputation: 198 Reputation: 198
Joined: 25 Jan 2006
Posts: 8517
Location: 127.0.0.1
|
 Posted: Thu Apr 06, 2017 11:00 pm Post subject: Posted: Thu Apr 06, 2017 11:00 pm Post subject: |
 |
|
Could try manually calling the NT function:
NtProtectVirtualMemory
If the target is protected see if they have a hook on VirtualProtect, if so you can just invoke it manually +5 from the start of the function in some cases. (You will have to account for the stack alignment and such when you do this.)
_________________
- Retired. |
|
| Back to top |
|
 |
Viloresi
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 02 Feb 2017
Posts: 149
|
 Posted: Fri Apr 07, 2017 12:43 am Post subject: Posted: Fri Apr 07, 2017 12:43 am Post subject: |
 |
|
Hey atomos , thank you for the reply.
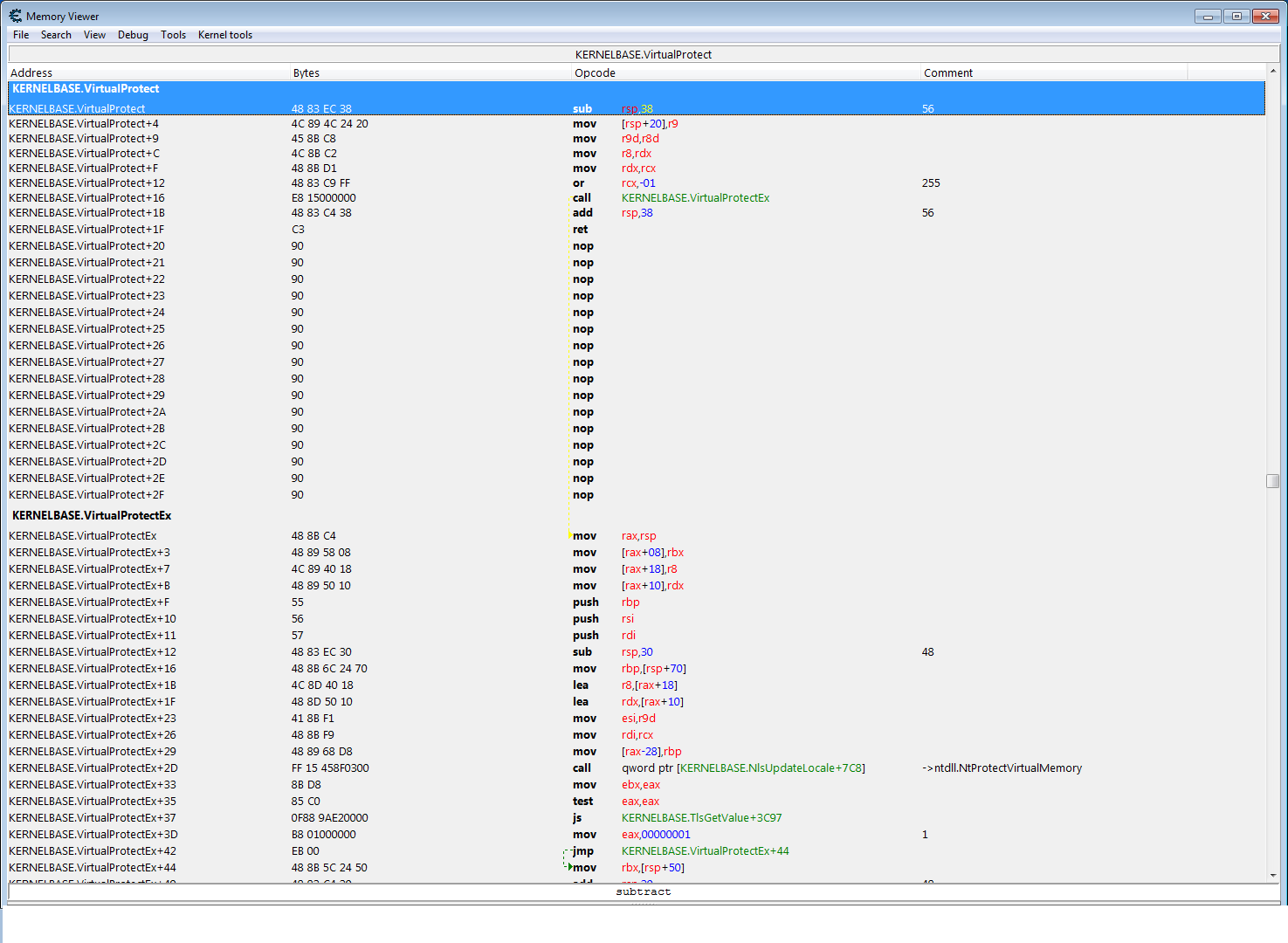
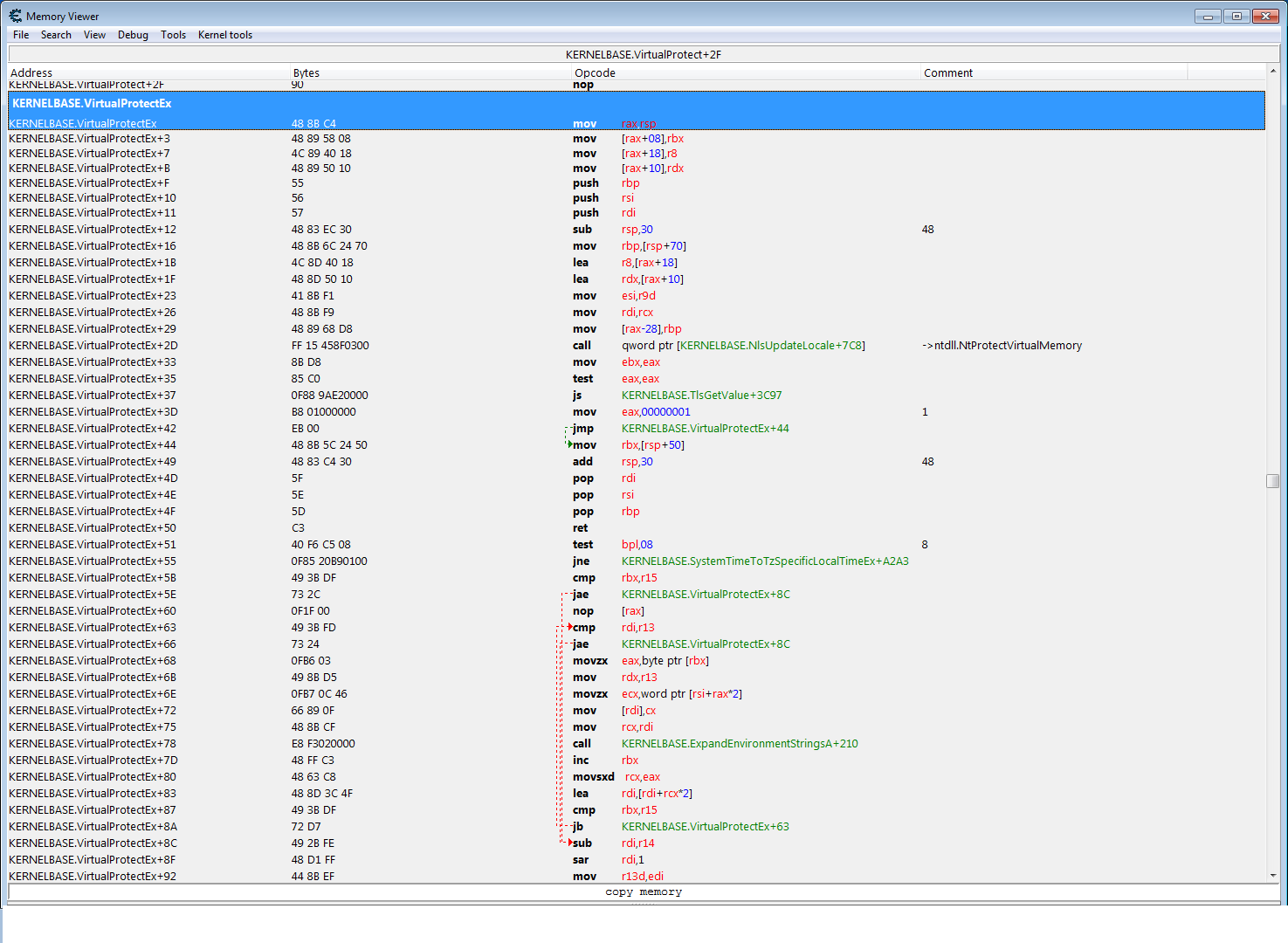
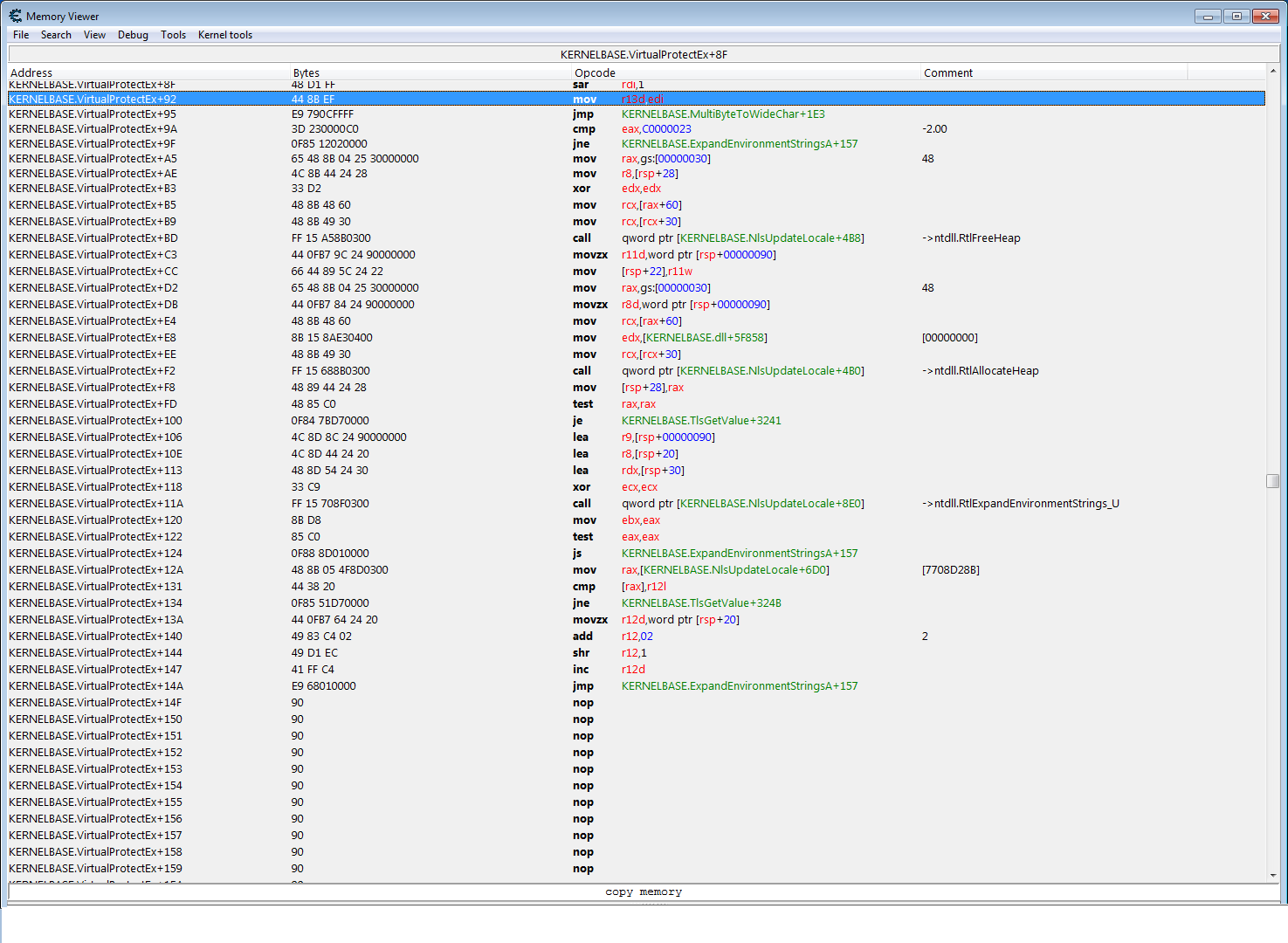
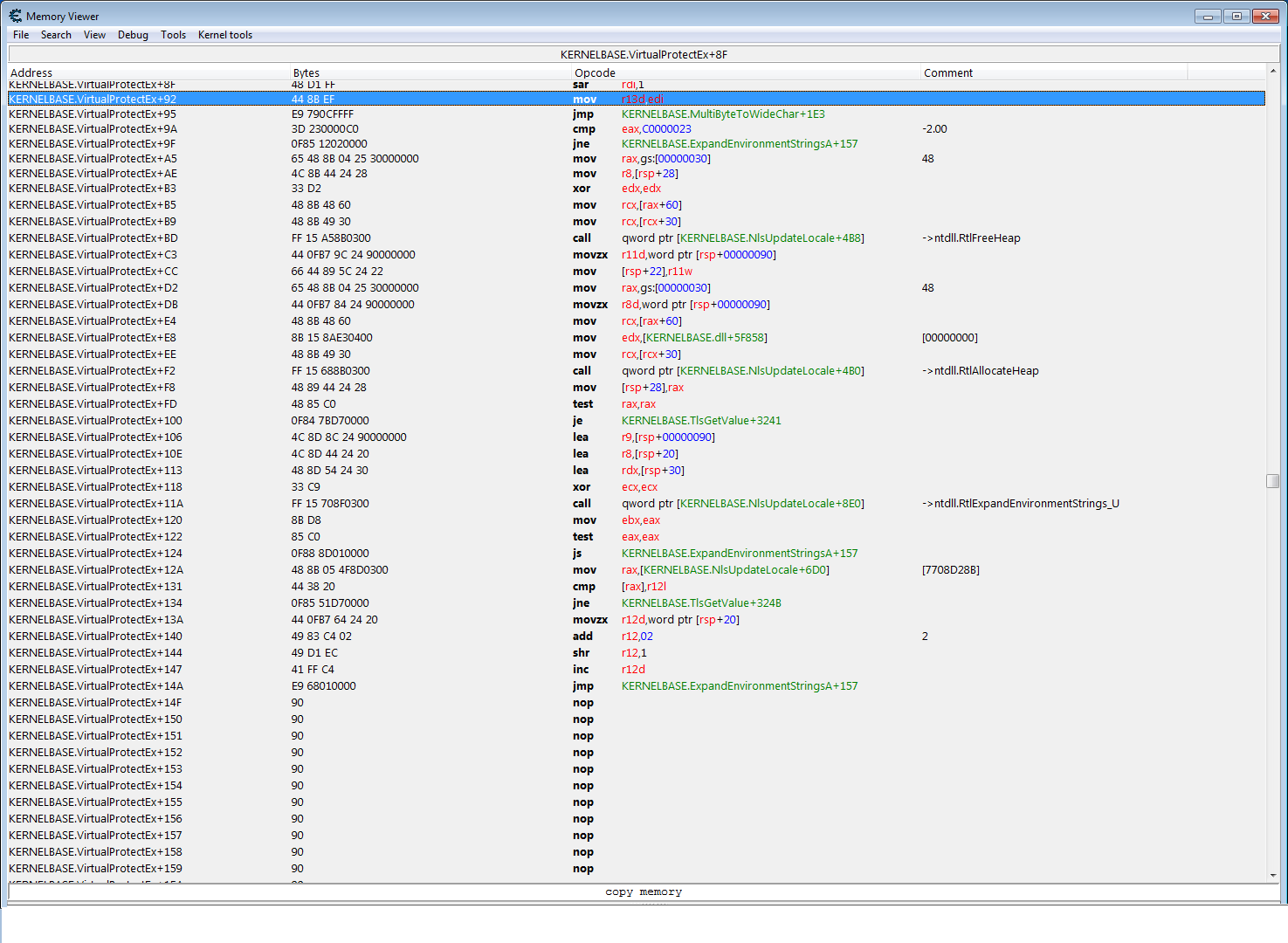
I've checked if the VirtualProtect has been hooked, but it's not, I've attached some screenshots of the function (atleast I hope is what you told me to check).
How should I do the call? How can I pass the 4 parameters (Handle ,BaseAddress, ProtectSize , NewProtection, Oldprotection ) and then call it?
I mean I don't know how to use the NtProtectVirtualMemory alone without the use of the kernel32 VirtualProtect.
Thank you!
Also I've forgot to mention that I'm trying this from an injected dll (but I think you already guessed it probably)
| Description: |
|
| Filesize: |
84.59 KB |
| Viewed: |
16115 Time(s) |
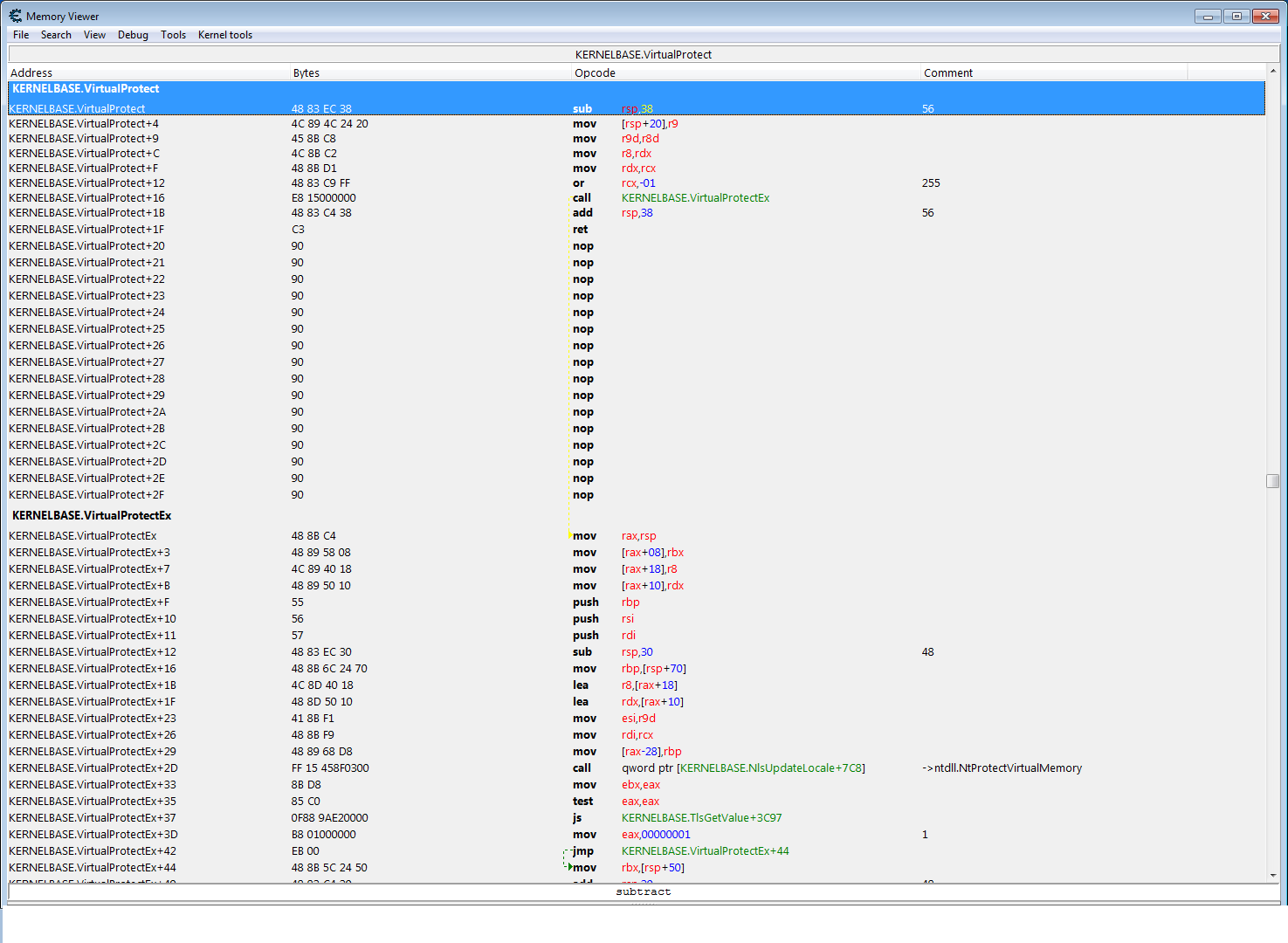
|
| Description: |
|
| Filesize: |
96.61 KB |
| Viewed: |
16115 Time(s) |
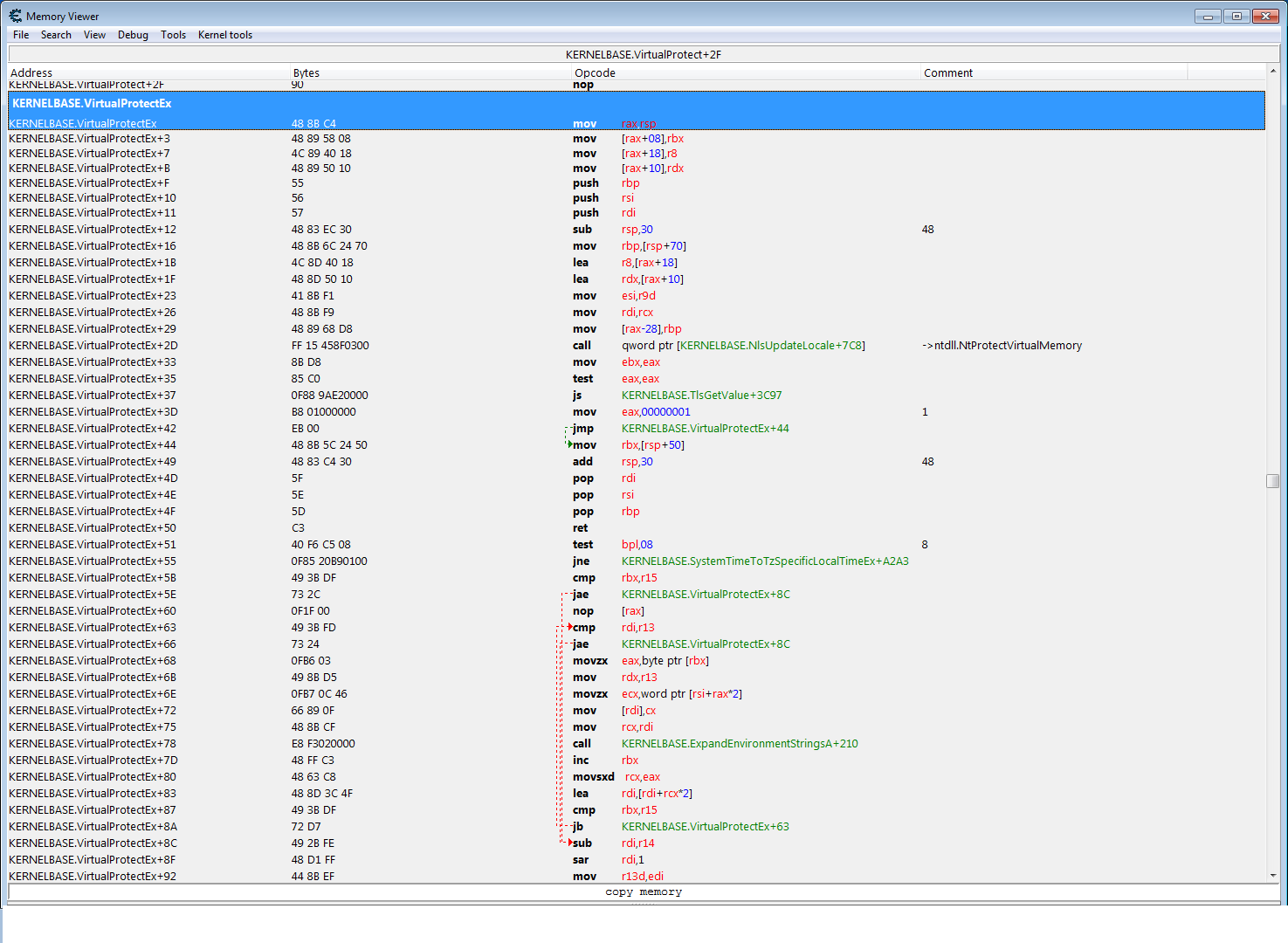
|
| Description: |
|
| Filesize: |
102.92 KB |
| Viewed: |
16115 Time(s) |
|
|
|
| Back to top |
|
 |
Dark Byte
Site Admin
 Reputation: 458 Reputation: 458
Joined: 09 May 2003
Posts: 25288
Location: The netherlands
|
 Posted: Fri Apr 07, 2017 3:19 am Post subject: Posted: Fri Apr 07, 2017 3:19 am Post subject: |
 |
|
perhaps ntProtectVirtualMemory is hooked
anyhow if all else fIls, use kernelmode
_________________
Do not ask me about online cheats. I don't know any and wont help finding them.
Like my help? Join me on Patreon so i can keep helping |
|
| Back to top |
|
 |
Viloresi
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 02 Feb 2017
Posts: 149
|
 Posted: Fri Apr 07, 2017 3:28 am Post subject: Posted: Fri Apr 07, 2017 3:28 am Post subject: |
 |
|
| Dark Byte wrote: | perhaps ntProtectVirtualMemory is hooked
anyhow if all else fIls, use kernelmode |
Thank you for the reply darkbyte...
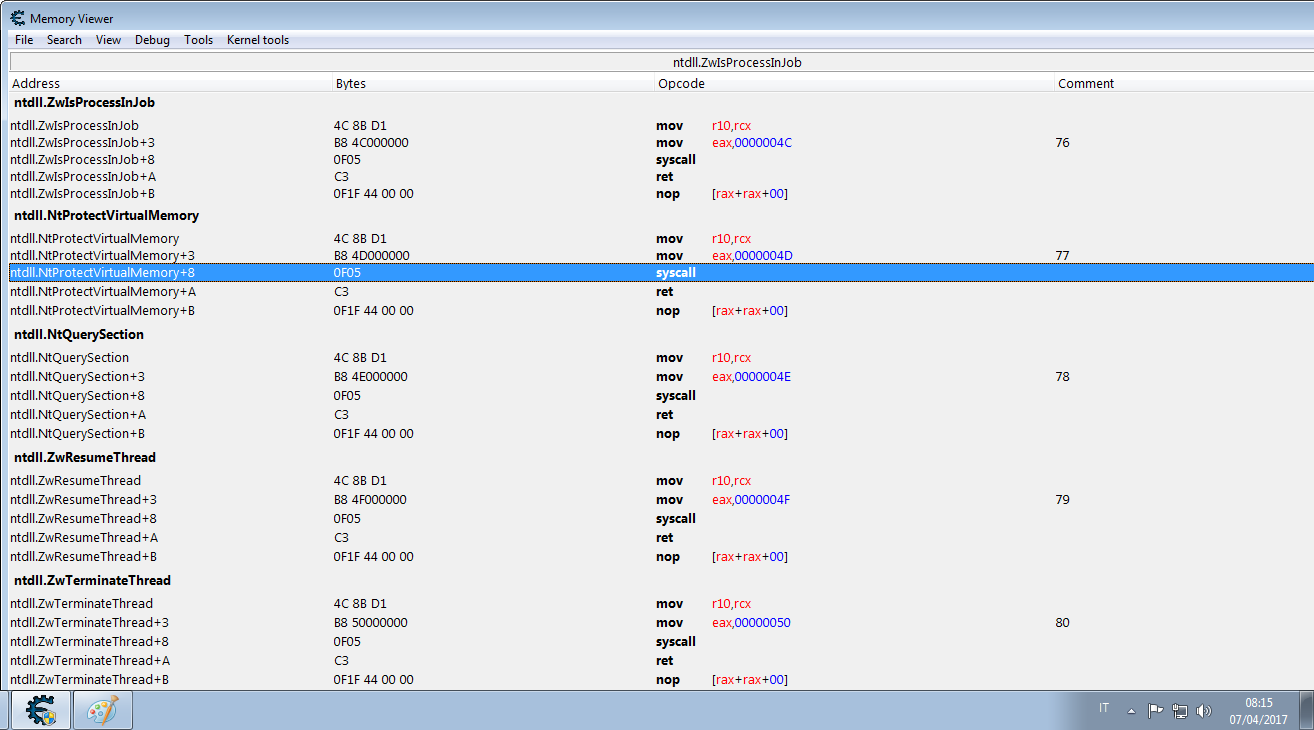
I've tried to check if ntProtectVirtualMemory is hooked too, but it doesn't seem to be...
btw I'm trying to do it in c++ from an injected dll, because I've already tried to change that address with cheat engine but nothing happens . (but it's not my point aniway since cheat engine is somehow detected).
I'm not 100% sure that I got what you meant , if you suggested me to use a driver to run this ;/ I may want to find another solution first if it's possible, I'm sure that atomos had a great idea, but I just don't know how to call the ntProtectVirtualMemory and pass it the parameters I need...
Thank you for the help guys
| Description: |
|
| Filesize: |
54.34 KB |
| Viewed: |
16100 Time(s) |
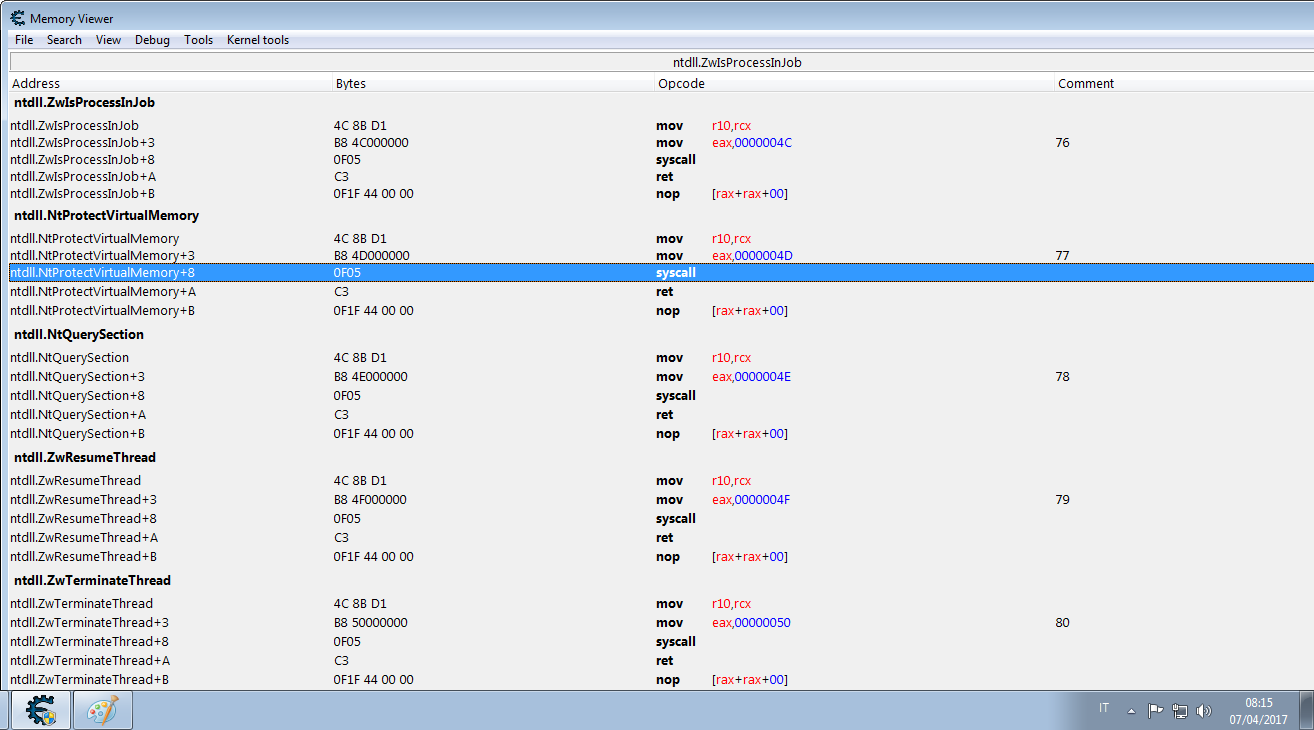
|
|
|
| Back to top |
|
 |
Viloresi
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 02 Feb 2017
Posts: 149
|
 Posted: Mon Apr 10, 2017 3:51 am Post subject: Posted: Mon Apr 10, 2017 3:51 am Post subject: |
 |
|
Up
Atomos or somebody knows how to use the NtProtectVirtualMemory?
I mean this function is undocumented, please if someone knows how to call it, it would be much appreciated since it could be a chance to bypass that protection.
|
|
| Back to top |
|
 |
atom0s
Moderator
 Reputation: 198 Reputation: 198
Joined: 25 Jan 2006
Posts: 8517
Location: 127.0.0.1
|
 Posted: Mon Apr 10, 2017 2:17 pm Post subject: Posted: Mon Apr 10, 2017 2:17 pm Post subject: |
 |
|
You can find sites like the following that give details on it:
https://undocumented.ntinternals.net/
Or just Google (or search Github) for the API name itself to find examples around the web.
_________________
- Retired. |
|
| Back to top |
|
 |
Viloresi
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 02 Feb 2017
Posts: 149
|
 Posted: Mon Apr 10, 2017 2:32 pm Post subject: Posted: Mon Apr 10, 2017 2:32 pm Post subject: |
 |
|
Thank you atomos, I knew that you are the best!
I've found it in the site that you gave me... Altough it's loaded from a dll, I've seen it uses the same parameters as the virtualprotect standard func .... But I still don't get why VirtualProtect calls this NtProtectVirtualMemory :S.
Aniway I'll try it, and if it bypass the protection I'll give a reply.
|
|
| Back to top |
|
 |
Viloresi
Expert Cheater
![]() Reputation: 0 Reputation: 0
Joined: 02 Feb 2017
Posts: 149
|
 Posted: Thu Apr 13, 2017 10:31 am Post subject: Posted: Thu Apr 13, 2017 10:31 am Post subject: |
 |
|
I've found the type of protection, (the ntdll functions don't work either btw)
for what I've discovered, they've used an undocumented flag named
" SEC_NO_CHANGE " to map the memory.
so one method to fix this is by re-mapping the views you are interested in (alloc new memory, copy, suspend , resume exc) ...
Can't tell more because I don't want to get anybody in troubles.
Btw I hope whoever was interested in this (or will be) now has an idea of what's the kind of protection.
(initially I tought about DEP or some other weird stuff, but it's not luckily)
|
|
| Back to top |
|
 |
atom0s
Moderator
 Reputation: 198 Reputation: 198
Joined: 25 Jan 2006
Posts: 8517
Location: 127.0.0.1
|
 Posted: Thu Apr 13, 2017 5:50 pm Post subject: Posted: Thu Apr 13, 2017 5:50 pm Post subject: |
 |
|
If you are getting to that point, a driver may be of interest for bypassing or altering how things are done. Rather than allowing it to create the memory with 'SEC_NO_CHANGE', alter it to be a different flag that gives you access and allows VirtualProtect and other userland calls to work fine.
Keep in mind it is very easy for a game to monitor changes to things such as page access, a checksum on the memory as well as checking for hooks made to any function userland or not. And given the target you are going after based on your pm to me, I would tread with caution for legal purposes as well.
_________________
- Retired. |
|
| Back to top |
|
 |
|

 Reputation: 198
Reputation: 198 Reputation: 458
Reputation: 458 Reputation: 198
Reputation: 198 Reputation: 198
Reputation: 198